Kb2467173 Download
Download Asmwsoft PC Optimizer software, and install it on your computer, and follow the steps bellow. 1- How to Stop kb2467173.exe process. Run Asmwsoft Pc Optimizer application. 2- How to remove kb2467173.exe from windows startup. From Asmwsoft Pc Optimizer main window select 'Startup manager' tool. To continue, you must first add this website to your trusted sites in Internet Explorer. The site cannot determine which updates apply to your computer or display those updates unless you change your security settings to allow ActiveX controls and active scripting. HerdProtect antiviru scan for the file kb2467173.exe (SHA-1 b19211187caa726619fefd80f199bf7df3266bb7). 0 of 68 malware scanners detected the file kb2467173.exe from. We and our AD Partners use cookies to understand how you use our site, improve your experience and serve you personalized content and advertising.
- Microsoft Security Update (kb2467173) Download
- Ms11 025 Fix
- Kb2467173 Download
- Kb2467173 Download Windows 10
- Kb2467173 Download
- I am running windows XP3 and all updates are current except for KB2467173.I tried downloading the file and install from desktop,I have cleared the Temp.files,download file,cache all to no avail.Following is my log,any help would be greatly appreciated.
- HerdProtect antiviru scan for the file kb2467173.exe (SHA-1 b19211187caa726619fefd80f199bf7df3266bb7). 0 of 68 malware scanners detected the file kb2467173.exe from.
- KB2467173 x64 Regarding KB2467173 which was just released (Microsoft Visual C++ 2010 RTM Redistributable MFC Security Update), apparently there was substantial vulnerabilities and subsequently fixes in both the x86 and x64 versions of VC++2010 but the download page only links to the x86 version.
Published: April 12, 2011 Updated: October 26, 2011
Version: 6.1
This bulletin summary lists security bulletins released for April 2011.
With the release of the security bulletins for April 2011, this bulletin summary replaces the bulletin advance notification originally issued April 7, 2011. For more information about the bulletin advance notification service, see Microsoft Security Bulletin Advance Notification.
For information about how to receive automatic notifications whenever Microsoft security bulletins are issued, visit Microsoft Technical Security Notifications.
Microsoft is hosting a webcast to address customer questions on these bulletins on April 13, 2011, at 11:00 AM Pacific Time (US & Canada). Register now for the April Security Bulletin Webcast. After this date, this webcast is available on-demand. For more information, see Microsoft Security Bulletin Summaries and Webcasts.
Microsoft also provides information to help customers prioritize monthly security updates with any non-security updates that are being released on the same day as the monthly security updates. Please see the section, Other Information.
Bulletin Information
Executive Summaries
The following table summarizes the security bulletins for this month in order of severity.
For details on affected software, see the next section, Affected Software and Download Locations.
| Bulletin ID | Bulletin Title and Executive Summary | Maximum Severity Rating and Vulnerability Impact | Restart Requirement | Affected Software |
|---|---|---|---|---|
| [MS11-018](http://go.microsoft.com/fwlink/?linkid=214126) | **Cumulative Security Update for Internet Explorer (2497640)** This security update resolves four privately reported vulnerabilities and one publicly disclosed vulnerability in Internet Explorer. This security update is rated Critical for Internet Explorer 6, Internet Explorer 7, and Internet Explorer 8 on Windows clients; and Moderate for Internet Explorer 6, Internet Explorer 7, and Internet Explorer 8 on Windows servers. Internet Explorer 9 is not affected by the vulnerabilities. The most severe vulnerabilities could allow remote code execution if a user views a specially crafted Web page using Internet Explorer. An attacker who successfully exploited any of these vulnerabilities could gain the same user rights as the local user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights. | [Critical](http://go.microsoft.com/fwlink/?linkid=21140) Remote Code Execution | Requires restart | Microsoft Windows, Internet Explorer |
| [MS11-019](http://go.microsoft.com/fwlink/?linkid=212314) | **Vulnerabilities in SMB Client Could Allow Remote Code Execution (2511455)** This security update resolves one publicly disclosed vulnerability and one privately reported vulnerability in Microsoft Windows. The more severe of these vulnerabilities could allow remote code execution if an attacker sent a specially crafted SMB response to a client-initiated SMB request. To exploit the vulnerability, an attacker must convince the user to initiate an SMB connection to a specially crafted SMB server. | [Critical](http://go.microsoft.com/fwlink/?linkid=21140) Remote Code Execution | Requires restart | Microsoft Windows |
| [MS11-020](http://go.microsoft.com/fwlink/?linkid=212236) | **Vulnerability in SMB Server Could Allow Remote Code Execution (2508429)** This security update resolves a privately reported vulnerability in Microsoft Windows. The vulnerability could allow remote code execution if an attacker created a specially crafted SMB packet and sent the packet to an affected system. Firewall best practices and standard default firewall configurations can help protect networks from attacks originating outside the enterprise perimeter that would attempt to exploit these vulnerabilities. | [Critical](http://go.microsoft.com/fwlink/?linkid=21140) Remote Code Execution | Requires restart | Microsoft Windows |
| [MS11-027](http://go.microsoft.com/fwlink/?linkid=214005) | **Cumulative Security Update of ActiveX Kill Bits (2508272)** This security update resolves two privately reported vulnerabilities and one publicly disclosed vulnerability in Microsoft software. The vulnerabilities could allow remote code execution if a user views a specially crafted Web page that instantiates a specific ActiveX control with Internet Explorer. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights. This update also includes kill bits for three third-party ActiveX controls. | [Critical](http://go.microsoft.com/fwlink/?linkid=21140) Remote Code Execution | May require restart | Microsoft Windows |
| [MS11-028](http://go.microsoft.com/fwlink/?linkid=207931) | **Vulnerability in .NET Framework Could Allow Remote Code Execution (2484015)** This security update resolves a publicly disclosed vulnerability in Microsoft .NET Framework. The vulnerability could allow remote code execution on a client system if a user views a specially crafted Web page using a Web browser that can run XAML Browser Applications (XBAPs). Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights. The vulnerability could also allow remote code execution on a server system running IIS, if that server allows processing ASP.NET pages and an attacker succeeds in uploading a specially crafted ASP.NET page to that server and then executes the page, as could be the case in a Web hosting scenario. This vulnerability could also be used by Windows .NET applications to bypass Code Access Security (CAS) restrictions. | [Critical](http://go.microsoft.com/fwlink/?linkid=21140) Remote Code Execution | May require restart | Microsoft Windows |
| [MS11-029](http://go.microsoft.com/fwlink/?linkid=208524) | **Vulnerability in GDI+ Could Allow Remote Code Execution (2489979)** This security update resolves a privately reported vulnerability in Microsoft Windows GDI+. The vulnerability could allow remote code execution if a user viewed a specially crafted image file using affected software or browsed a Web site that contains specially crafted content. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights. | [Critical](http://go.microsoft.com/fwlink/?linkid=21140) Remote Code Execution | May require restart | Microsoft Windows, Microsoft Office |
| [MS11-030](http://go.microsoft.com/fwlink/?linkid=212595) | **Vulnerability in DNS Resolution Could Allow Remote Code Execution (2509553)** This security update resolves a privately reported vulnerability in Windows DNS resolution. The vulnerability could allow remote code execution if an attacker gained access to the network and then created a custom program to send specially crafted LLMNR broadcast queries to the target systems. Firewall best practices and standard default firewall configurations can help protect networks from attacks that originate outside the enterprise perimeter. Best practices recommend that systems that are connected to the Internet have a minimal number of ports exposed. In this case, the LLMNR ports should be blocked from the Internet. | [Critical](http://go.microsoft.com/fwlink/?linkid=21140) Remote Code Execution | Requires restart | Microsoft Windows |
| [MS11-031](http://go.microsoft.com/fwlink/?linkid=212243) | **Vulnerability in JScript and VBScript Scripting Engines Could Allow Remote Code Execution (2514666)** This security update resolves a privately reported vulnerability in the JScript and VBScript scripting engines. The vulnerability could allow remote code execution if a user visited a specially crafted Web site. An attacker would have no way to force users to visit the Web site. Instead, an attacker would have to convince users to visit the Web site, typically by getting them to click a link in an e-mail message or Instant Messenger message that takes users to the attacker's Web site. | [Critical](http://go.microsoft.com/fwlink/?linkid=21140) Remote Code Execution | May require restart | Microsoft Windows |
| [MS11-032](http://go.microsoft.com/fwlink/?linkid=212224) | **Vulnerability in the OpenType Compact Font Format (CFF) Driver Could Allow Remote Code Execution (2507618)** This security update resolves a privately reported vulnerability in the OpenType Compact Font Format (CFF) driver. The vulnerability could allow remote code execution if a user views content rendered in a specially crafted CFF font. In all cases, an attacker would have no way to force users to view the specially crafted content. Instead, an attacker would have to convince users to visit a Web site, typically by getting them to click a link in an e-mail message or Instant Messenger message that takes users to the attacker's Web site. | [Critical](http://go.microsoft.com/fwlink/?linkid=21140) Remote Code Execution | Requires restart | Microsoft Windows |
| [MS11-021](http://go.microsoft.com/fwlink/?linkid=210121) | **Vulnerabilities in Microsoft Excel Could Allow Remote Code Execution (2489279)** This security update resolves nine privately reported vulnerabilities in Microsoft Office. The vulnerabilities could allow remote code execution if a user opens a specially crafted Excel file. An attacker who successfully exploited any of these vulnerabilities could gain the same user rights as the logged-on user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights. | [Important](http://go.microsoft.com/fwlink/?linkid=21140) Remote Code Execution | May require restart | Microsoft Office |
| [MS11-022](http://go.microsoft.com/fwlink/?linkid=210727) | **Vulnerabilities in Microsoft PowerPoint Could Allow Remote Code Execution (2489283)** This security update resolves three privately reported vulnerabilities in Microsoft PowerPoint. The vulnerabilities could allow remote code execution if a user opens a specially crafted PowerPoint file. An attacker who successfully exploited any of these vulnerabilities could gain the same user rights as the local user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights. The automated **Microsoft Fix it** solution for PowerPoint 2010, 'Disable Edit in Protected View for PowerPoint 2010,' available in [Microsoft Knowledge Base Article 2501584](http://support.microsoft.com/kb/2501584) , blocks the attack vectors for exploiting the vulnerabilities described in CVE-2011-0655 and CVE-2011-0656. | [Important](http://go.microsoft.com/fwlink/?linkid=21140) Remote Code Execution | May require restart | Microsoft Office, Microsoft Server Software |
| [MS11-023](http://go.microsoft.com/fwlink/?linkid=210206) | **Vulnerabilities in Microsoft Office Could Allow Remote Code Execution (2489293)** This security update resolves one publicly disclosed vulnerability and one privately reported vulnerability in Microsoft Office. The vulnerabilities could allow remote code execution if a user opens a specially crafted Office file or if a user opens a legitimate Office file that is located in the same network directory as a specially crafted library file. An attacker who successfully exploited either of these vulnerabilities could gain the same user rights as the logged on user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights. | [Important](http://go.microsoft.com/fwlink/?linkid=21140) Remote Code Execution | May require restart | Microsoft Office |
| [MS11-024](http://go.microsoft.com/fwlink/?linkid=212226) | **Vulnerabilities in Windows Fax Cover Page Editor Could Allow Remote Code Execution (2527308)** This security update resolves two publicly disclosed vulnerabilities in Microsoft Windows. The vulnerabilities could allow remote code execution if a user opened a specially crafted fax cover page file (.cov) using the Windows Fax Cover Page Editor. An attacker who successfully exploited either of these vulnerabilities could gain the same user rights as the logged-on user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights. | [Important](http://go.microsoft.com/fwlink/?linkid=21140) Remote Code Execution | May require restart | Microsoft Windows |
| [MS11-025](http://go.microsoft.com/fwlink/?linkid=209720) | **Vulnerability in Microsoft Foundation Class (MFC) Library Could Allow Remote Code Execution (2500212)** This security update resolves a publicly disclosed vulnerability in certain applications built using the Microsoft Foundation Class (MFC) Library. The vulnerability could allow remote code execution if a user opens a legitimate file associated with such an affected application, and the file is located in the same network folder as a specially crafted library file. For an attack to be successful, a user must visit an untrusted remote file system location or WebDAV share and open a document from this location that is then loaded by the affected application. | [Important](http://go.microsoft.com/fwlink/?linkid=21140) Remote Code Execution | May require restart | Microsoft Developer Tools and Software |
| [MS11-026](http://go.microsoft.com/fwlink/?linkid=212523) | **Vulnerability in MHTML Could Allow Information Disclosure (2503658)** This security update resolves a publicly disclosed vulnerability in the MHTML protocol handler in Microsoft Windows. The vulnerability could allow information disclosure if a user visited a specially crafted Web site. In a Web-based attack scenario, a Web site could contain a specially crafted link that is used to exploit this vulnerability. An attacker would have to convince users to visit the Web site and open the specially crafted link. | [Important](http://go.microsoft.com/fwlink/?linkid=21140) Information Disclosure | Requires restart | Microsoft Windows |
| [MS11-033](http://go.microsoft.com/fwlink/?linkid=208110) | **Vulnerability in WordPad Text Converters Could Allow Remote Code Execution (2485663)** This security update resolves a privately reported vulnerability in Microsoft Windows. This security update is rated Important for all supported editions of Windows XP and Windows Server 2003. All supported editions of Windows Vista, Windows Server 2008, Windows 7, and Windows Server 2008 R2 are not affected by the vulnerability. The vulnerability could allow remote code execution if a user opened a specially crafted file using WordPad. An attacker who successfully exploited this vulnerability could gain the same user rights as the local user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights. | [Important](http://go.microsoft.com/fwlink/?linkid=21140) Remote Code Execution | May require restart | Microsoft Windows |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | **Vulnerabilities in Windows Kernel-Mode Drivers Could Allow Elevation of Privilege (2506223)** This security update resolves thirty privately reported vulnerabilities in Microsoft Windows. The vulnerabilities could allow elevation of privilege if an attacker logged on locally and ran a specially crafted application. An attacker must have valid logon credentials and be able to log on locally to exploit these vulnerabilities. The vulnerabilities could not be exploited remotely or by anonymous users. | [Important](http://go.microsoft.com/fwlink/?linkid=21140) Elevation of Privilege | Requires restart | Microsoft Windows |
Exploitability Index
The following table provides an exploitability assessment of each of the vulnerabilities addressed this month. The vulnerabilities are listed in order of decreasing exploitability assessment level then CVE ID. Only vulnerabilities that have a severity rating of Critical or Important in the bulletins are included.
How do I use this table?
Use this table to learn about the likelihood of functioning exploit code being released within 30 days of security bulletin release, for each of the security updates that you may need to install. You should review each of the assessments below, in accordance with your specific configuration, in order to prioritize your deployment. For more information about what these ratings mean, and how they are determined, please see Microsoft Exploitability Index.
| Bulletin ID | Vulnerability Title | CVE ID | Exploitability Index Assessment | Key Notes |
|---|---|---|---|---|
| [MS11-025](http://go.microsoft.com/fwlink/?linkid=209720) | MFC Insecure Library Loading Vulnerability | [CVE-2010-3190](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2010-3190) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | This vulnerability has been disclosed publicly |
| [MS11-028](http://go.microsoft.com/fwlink/?linkid=207931) | .NET Framework Stack Corruption Vulnerability | [CVE-2010-3958](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2010-3958) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | This vulnerability has been disclosed publicly |
| [MS11-032](http://go.microsoft.com/fwlink/?linkid=212224) | OpenType Font Stack Overflow Vulnerability | [CVE-2011-0034](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0034) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-029](http://go.microsoft.com/fwlink/?linkid=208524) | GDI+ Integer Overflow Vulnerability | [CVE-2011-0041](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0041) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-018](http://go.microsoft.com/fwlink/?linkid=214126) | Layouts Handling Memory Corruption Vulnerability | [CVE-2011-0094](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0094) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | **This vulnerability is being exploited in limited, targeted attacks** |
| [MS11-021](http://go.microsoft.com/fwlink/?linkid=210121) | Excel Integer Overrun Vulnerability | [CVE-2011-0097](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0097) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-021](http://go.microsoft.com/fwlink/?linkid=210121) | Excel Heap Overflow Vulnerability | [CVE-2011-0098](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0098) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-021](http://go.microsoft.com/fwlink/?linkid=210121) | Excel Record Parsing WriteAV Vulnerability | [CVE-2011-0101](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0101) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-023](http://go.microsoft.com/fwlink/?linkid=210206) | Office Component Insecure Library Loading Vulnerability | [CVE-2011-0107](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0107) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | This vulnerability has been disclosed publicly |
| [MS11-018](http://go.microsoft.com/fwlink/?linkid=214126) | MSHTML Memory Corruption Vulnerability | [CVE-2011-0346](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0346) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | This vulnerability has been disclosed publicly |
| [MS11-019](http://go.microsoft.com/fwlink/?linkid=212314) | SMB Client Response Parsing Vulnerability | [CVE-2011-0660](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0660) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-020](http://go.microsoft.com/fwlink/?linkid=212236) | SMB Transaction Parsing Vulnerability | [CVE-2011-0661](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0661) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Use After Free Vulnerability | [CVE-2011-0662](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0662) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Use After Free Vulnerability | [CVE-2011-0665](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0665) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Use After Free Vulnerability | [CVE-2011-0666](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0666) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Use After Free Vulnerability | [CVE-2011-0667](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0667) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Use After Free Vulnerability | [CVE-2011-0670](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0670) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Use After Free Vulnerability | [CVE-2011-0671](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0671) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Use After Free Vulnerability | [CVE-2011-0672](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0672) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Null Pointer De-reference Vulnerability | [CVE-2011-0673](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0673) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Use After Free Vulnerability | [CVE-2011-0674](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0674) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Use After Free Vulnerability | [CVE-2011-0675](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0675) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Null Pointer De-reference Vulnerability | [CVE-2011-0676](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0676) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Null Pointer De-reference Vulnerability | [CVE-2011-0677](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0677) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-022](http://go.microsoft.com/fwlink/?linkid=210727) | OfficeArt Atom RCE Vulnerability | [CVE-2011-0976](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0976) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-021](http://go.microsoft.com/fwlink/?linkid=210121) | Excel Array Indexing Vulnerability | [CVE-2011-0978](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0978) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-021](http://go.microsoft.com/fwlink/?linkid=210121) | Excel Linked List Corruption Vulnerability | [CVE-2011-0979](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0979) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-021](http://go.microsoft.com/fwlink/?linkid=210121) | Excel Dangling Pointer Vulnerability | [CVE-2011-0980](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0980) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Null Pointer De-reference Vulnerability | [CVE-2011-1225](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1225) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Null Pointer De-reference Vulnerability | [CVE-2011-1226](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1226) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Null Pointer De-reference Vulnerability | [CVE-2011-1227](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1227) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Null Pointer De-reference Vulnerability | [CVE-2011-1228](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1228) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Null Pointer De-reference Vulnerability | [CVE-2011-1229](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1229) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Null Pointer De-reference Vulnerability | [CVE-2011-1230](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1230) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Null Pointer De-reference Vulnerability | [CVE-2011-1231](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1231) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Null Pointer De-reference Vulnerability | [CVE-2011-1232](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1232) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Null Pointer De-reference Vulnerability | [CVE-2011-1233](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1233) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Use After Free Vulnerability | [CVE-2011-1235](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1235) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Use After Free Vulnerability | [CVE-2011-1236](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1236) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Use After Free Vulnerability | [CVE-2011-1237](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1237) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Use After Free Vulnerability | [CVE-2011-1239](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1239) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Use After Free Vulnerability | [CVE-2011-1240](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1240) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Use After Free Vulnerability | [CVE-2011-1241](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1241) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Use After Free Vulnerability | [CVE-2011-1242](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1242) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | (None) |
| [MS11-018](http://go.microsoft.com/fwlink/?linkid=214126) | Object Management Memory Corruption Vulnerability | [CVE-2011-1345](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1345) | [1](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Consistent exploit code likely | **This vulnerability is being exploited in limited, targeted attacks** |
| [MS11-033](http://go.microsoft.com/fwlink/?linkid=208110) | WordPad Converter Parsing Vulnerability | [CVE-2011-0028](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0028) | [2](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Inconsistent exploit code likely | (None) |
| [MS11-021](http://go.microsoft.com/fwlink/?linkid=210121) | Excel Memory Corruption Vulnerability | [CVE-2011-0103](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0103) | [2](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Inconsistent exploit code likely | (None) |
| [MS11-021](http://go.microsoft.com/fwlink/?linkid=210121) | Excel Buffer Overwrite Vulnerability | [CVE-2011-0104](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0104) | [2](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Inconsistent exploit code likely | (None) |
| [MS11-021](http://go.microsoft.com/fwlink/?linkid=210121) | Excel Data Initialization Vulnerability | [CVE-2011-0105](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0105) | [2](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Inconsistent exploit code likely | (None) |
| [MS11-019](http://go.microsoft.com/fwlink/?linkid=212314) | Browser Pool Corruption Vulnerability | [CVE-2011-0654](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0654) | [2](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Inconsistent exploit code likely | This vulnerability has been disclosed publicly |
| [MS11-022](http://go.microsoft.com/fwlink/?linkid=210727) | Floating Point Techno-color Time Bandit RCE Vulnerability | [CVE-2011-0655](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0655) | [2](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Inconsistent exploit code likely | (None) |
| [MS11-022](http://go.microsoft.com/fwlink/?linkid=210727) | Persist Directory RCE Vulnerability | [CVE-2011-0656](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0656) | [2](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Inconsistent exploit code likely | (None) |
| [MS11-030](http://go.microsoft.com/fwlink/?linkid=212595) | DNS Query Vulnerability | [CVE-2011-0657](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0657) | [2](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Inconsistent exploit code likely | (None) |
| [MS11-031](http://go.microsoft.com/fwlink/?linkid=212243) | Scripting Memory Reallocation Vulnerability | [CVE-2011-0663](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0663) | [2](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Inconsistent exploit code likely | (None) |
| [MS11-023](http://go.microsoft.com/fwlink/?linkid=210206) | Microsoft Office Graphic Object Dereferencing Vulnerability | [CVE-2011-0977](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0977) | [2](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Inconsistent exploit code likely | (None) |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Use After Free Vulnerability | [CVE-2011-1234](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1234) | [2](http://technet.microsoft.com/en-us/security/cc998259.aspx) - Inconsistent exploit code likely | (None) |
| [MS11-024](http://go.microsoft.com/fwlink/?linkid=212226) | Fax Cover Page Editor Memory Corruption Vulnerability | [CVE-2010-3974](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2010-3974) | [3](http://technet.microsoft.com/en-us/security/cc998259.aspx) – Functioning exploit code unlikely | This vulnerability has been disclosed publicly |
| [MS11-024](http://go.microsoft.com/fwlink/?linkid=212226) | Fax Cover Page Use After Free Vulnerability | [CVE-2010-4701](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2010-4701) | [3](http://technet.microsoft.com/en-us/security/cc998259.aspx) – Functioning exploit code unlikely | This vulnerability has been disclosed publicly |
| [MS11-026](http://go.microsoft.com/fwlink/?linkid=212523) | MHTML Mime-Formatted Request Vulnerability | [CVE-2011-0096](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-0096) | [3](http://technet.microsoft.com/en-us/security/cc998259.aspx) – Functioning exploit code unlikely | This vulnerability has been disclosed publicly This is an information disclosure vulnerability |
| [MS11-034](http://go.microsoft.com/fwlink/?linkid=211826) | Win32k Use After Free Vulnerability | [CVE-2011-1238](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1238) | [3](http://technet.microsoft.com/en-us/security/cc998259.aspx) – Functioning exploit code unlikely | (None) |
| [MS11-018](http://go.microsoft.com/fwlink/?linkid=214126) | Javascript Information Disclosure Vulnerability | [CVE-2011-1245](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2011-1245) | [3](http://technet.microsoft.com/en-us/security/cc998259.aspx) – Functioning exploit code unlikely | This is an information disclosure vulnerability |
Affected Software and Download Locations ----------------------------------------
The following tables list the bulletins in order of major software category and severity.
How do I use these tables?
Use these tables to learn about the security updates that you may need to install. You should review each software program or component listed to see whether any security updates pertain to your installation. If a software program or component is listed, then the available software update is hyperlinked and the severity rating of the software update is also listed.
Note You may have to install several security updates for a single vulnerability. Review the whole column for each bulletin identifier that is listed to verify the updates that you have to install, based on the programs or components that you have installed on your system.
Windows Operating System and Components
| Windows XP | |||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| **Bulletin Identifier** | [**MS11-018**](http://go.microsoft.com/fwlink/?linkid=214126) | [**MS11-019**](http://go.microsoft.com/fwlink/?linkid=212314) | [**MS11-020**](http://go.microsoft.com/fwlink/?linkid=212236) | [**MS11-027**](http://go.microsoft.com/fwlink/?linkid=214005) | [**MS11-028**](http://go.microsoft.com/fwlink/?linkid=207931) | [**MS11-029**](http://go.microsoft.com/fwlink/?linkid=208524) | [**MS11-030**](http://go.microsoft.com/fwlink/?linkid=212595) | [**MS11-031**](http://go.microsoft.com/fwlink/?linkid=212243) | [**MS11-032**](http://go.microsoft.com/fwlink/?linkid=212224) | [**MS11-024**](http://go.microsoft.com/fwlink/?linkid=212226) | [**MS11-026**](http://go.microsoft.com/fwlink/?linkid=212523) | [**MS11-033**](http://go.microsoft.com/fwlink/?linkid=208110) | [**MS11-034**](http://go.microsoft.com/fwlink/?linkid=211826) |
| **Aggregate Severity Rating** | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) |
| Windows XP Service Pack 3 | [Internet Explorer 6](http://www.microsoft.com/downloads/details.aspx?familyid=c3a8cec0-f947-4d4e-a6ae-c7f4f1f311b0) (Critical) [Internet Explorer 7](http://www.microsoft.com/downloads/details.aspx?familyid=0b7d0403-8965-4c62-970c-20b561f66713) (Critical) [Internet Explorer 8](http://www.microsoft.com/downloads/details.aspx?familyid=689c5496-56c4-48a6-9f3d-b5f5aaf3e566) (Critical) | [Windows XP Service Pack 3](http://www.microsoft.com/downloads/details.aspx?familyid=f5378e7b-4619-4c42-9d9f-87b209c6d878) (Critical) | [Windows XP Service Pack 3](http://www.microsoft.com/downloads/details.aspx?familyid=ccb08a8a-f4d9-4320-8ffb-3fd4fe217987) (Critical) | [Windows XP Service Pack 3](http://www.microsoft.com/downloads/details.aspx?familyid=b031a496-aa74-4367-b2ae-24843c061745) (Critical) | [Microsoft .NET Framework 2.0 Service Pack 2 and Microsoft .NET Framework 3.5 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=ce925e76-cb85-48f6-8c0f-e53fa2b09be6) (KB2446704) (Critical) [Microsoft .NET Framework 4.0](http://www.microsoft.com/downloads/details.aspx?familyid=91aa6772-4811-4a58-9bc0-8aa271ed99df)[1](KB2446708) (Critical) | [Windows XP Service Pack 3](http://www.microsoft.com/downloads/details.aspx?familyid=59266a9d-a319-4309-a046-7f15c6da0136) (KB2412687) (Critical) | [Windows XP Service Pack 3](http://www.microsoft.com/downloads/details.aspx?familyid=2d433adb-bcaf-4c59-9405-a4892f8ccba3) (Important) | [JScript 5.7 and VBScript 5.7](http://www.microsoft.com/downloads/details.aspx?familyid=637f4d4c-de07-4c6a-95f8-3bd0cbfe77b2) (KB2510581) (Critical) [JScript 5.8 and VBScript 5.8](http://www.microsoft.com/downloads/details.aspx?familyid=fbe1e7e3-1d5f-4daf-a4a5-67fe79292963) (KB2510531) (Critical) | [Windows XP Service Pack 3](http://www.microsoft.com/downloads/details.aspx?familyid=9080c5a1-e638-4047-a70a-9367f1acced7) (Important) | [Windows XP Service Pack 3](http://www.microsoft.com/downloads/details.aspx?familyid=50fc3869-f2fc-43c8-8049-aad62f2cb332) (KB2491683) (Important) [Windows XP Service Pack 3](http://www.microsoft.com/downloads/details.aspx?familyid=a8220a21-02fc-4ad6-988d-844276b2fd66) (KB2506212) (Important) | [Windows XP Service Pack 3](http://www.microsoft.com/downloads/details.aspx?familyid=7f0a4616-8e3e-4925-9d95-ce6e614e45ae) (Important) | [Windows XP Service Pack 3](http://www.microsoft.com/downloads/details.aspx?familyid=6753ca98-feb4-4c7f-9969-9294038a2bbb) (Important) | [Windows XP Service Pack 3](http://www.microsoft.com/downloads/details.aspx?familyid=39e55bbf-c1c5-4696-bfe7-632e997cd98e) (Important) |
| Windows XP Professional x64 Edition Service Pack 2 | [Internet Explorer 6](http://www.microsoft.com/downloads/details.aspx?familyid=986f07ae-0fdc-4be2-8a74-5eb56d4300ef) (Critical) [Internet Explorer 7](http://www.microsoft.com/downloads/details.aspx?familyid=ed88f183-dd06-46f6-ae8a-a594a752f248) (Critical) [Internet Explorer 8](http://www.microsoft.com/downloads/details.aspx?familyid=6d3433ee-c2e1-433f-a3d9-c049d66e2190) (Critical) | [Windows XP Professional x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=c01441da-8933-4f60-923b-d9b00db8ba3d) (Critical) | [Windows XP Professional x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=7ee202da-a711-42ee-bea3-7202a70e4ea0) (Critical) | [Windows XP Professional x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=eddd2964-9765-461d-9df8-2c05402948e8) (Critical) | [Microsoft .NET Framework 2.0 Service Pack 2 and Microsoft .NET Framework 3.5 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=ce925e76-cb85-48f6-8c0f-e53fa2b09be6) (KB2446704) (Critical) [Microsoft .NET Framework 4.0](http://www.microsoft.com/downloads/details.aspx?familyid=91aa6772-4811-4a58-9bc0-8aa271ed99df)[1](KB2446708) (Critical) | [Windows XP Professional x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=3797009a-b9a4-4e83-8614-e1589c8b5090) (KB2412687) (Critical) | [Windows XP Professional x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=29ff546e-a232-4f23-a223-c029c71ff1c6) (Important) | [JScript 5.6 and VBScript 5.6](http://www.microsoft.com/downloads/details.aspx?familyid=a5586246-2908-4def-9298-c16060098197) (KB2510587) (Critical) [JScript 5.7 and VBScript 5.7](http://www.microsoft.com/downloads/details.aspx?familyid=3a5f65e0-bb00-4e55-b8b5-77751349a3ec) (KB2510581) (Critical) [JScript 5.8 and VBScript 5.8](http://www.microsoft.com/downloads/details.aspx?familyid=57aa7ee2-254d-40b5-9ff0-cba969daf45a) (KB2510531) (Critical) | [Windows XP Professional x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=2374e09a-cb3e-4bc3-bb4b-53b611025121) (Important) | [Windows XP Professional x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=b93311b4-1b8f-478d-8833-750c5e01e6f8) (KB2491683) (Important) [Windows XP Professional x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=0f60fc99-cd88-4237-8b31-a4e618502f7e) (KB2506212) (Important) | [Windows XP Professional x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=b01fe9a5-66a4-4683-963b-e78aea214579) (Important) | [Windows XP Professional x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=3c94bc96-99ea-44a1-9052-e69de5e21f81) (Important) | [Windows XP Professional x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=83771177-284e-4918-86a9-980e8229c7c9) (Important) |
| Windows Server 2003 | |||||||||||||
| **Bulletin Identifier** | [**MS11-018**](http://go.microsoft.com/fwlink/?linkid=214126) | [**MS11-019**](http://go.microsoft.com/fwlink/?linkid=212314) | [**MS11-020**](http://go.microsoft.com/fwlink/?linkid=212236) | [**MS11-027**](http://go.microsoft.com/fwlink/?linkid=214005) | [**MS11-028**](http://go.microsoft.com/fwlink/?linkid=207931) | [**MS11-029**](http://go.microsoft.com/fwlink/?linkid=208524) | [**MS11-030**](http://go.microsoft.com/fwlink/?linkid=212595) | [**MS11-031**](http://go.microsoft.com/fwlink/?linkid=212243) | [**MS11-032**](http://go.microsoft.com/fwlink/?linkid=212224) | [**MS11-024**](http://go.microsoft.com/fwlink/?linkid=212226) | [**MS11-026**](http://go.microsoft.com/fwlink/?linkid=212523) | [**MS11-033**](http://go.microsoft.com/fwlink/?linkid=208110) | [**MS11-034**](http://go.microsoft.com/fwlink/?linkid=211826) |
| **Aggregate Severity Rating** | [**Moderate**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Moderate**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Low**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) |
| Windows Server 2003 Service Pack 2 | [Internet Explorer 6](http://www.microsoft.com/downloads/details.aspx?familyid=b902c58a-9e2f-4352-8d2f-fffda5344598) (Moderate) [Internet Explorer 7](http://www.microsoft.com/downloads/details.aspx?familyid=5c464287-3dab-4342-a38d-a12719d3b158) (Moderate) [Internet Explorer 8](http://www.microsoft.com/downloads/details.aspx?familyid=45feb35b-b24e-4160-adb0-d0b7ae530e90) (Moderate) | [Windows Server 2003 Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=d46fe0bf-28c2-4696-87bc-dd3c8287fc28) (Critical) | [Windows Server 2003 Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=64c550d4-c927-4382-91e1-473ed6790819) (Critical) | [Windows Server 2003 Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=53756404-39e4-43af-81e9-81471536aa66) (Moderate) | [Microsoft .NET Framework 2.0 Service Pack 2 and Microsoft .NET Framework 3.5 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=ce925e76-cb85-48f6-8c0f-e53fa2b09be6) (KB2446704) (Critical) [Microsoft .NET Framework 4.0](http://www.microsoft.com/downloads/details.aspx?familyid=91aa6772-4811-4a58-9bc0-8aa271ed99df)[1](KB2446708) (Critical) | [Windows Server 2003 Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=fd284233-e177-4064-9b02-f83dcb727dbe) (KB2412687) (Critical) | [Windows Server 2003 Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=753ed6e3-df2e-4b2d-9e9f-7275cd94d214) (Important) | [JScript 5.6 and VBScript 5.6](http://www.microsoft.com/downloads/details.aspx?familyid=e026f2ed-8a20-4268-9b29-04a78bde1999) (KB2510587) (Critical) [JScript 5.7 and VBScript 5.7](http://www.microsoft.com/downloads/details.aspx?familyid=5b0ed0b2-07f9-43da-bb5d-5be5a45969ee) (KB2510581) (Critical) [JScript 5.8 and VBScript 5.8](http://www.microsoft.com/downloads/details.aspx?familyid=01aa2beb-9fc1-40f0-a2a4-bcd3d9cb31f8) (KB2510531) (Critical) | [Windows Server 2003 Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=5d71d3f5-fd6b-4f3b-8389-37c899748d4b) (Important) | [Windows Server 2003 Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=edda8cce-b764-4ef1-afbe-391fbd087362) (KB2491683) (Important) [Windows Server 2003 Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=bf084b4c-aac9-4cc6-bb30-87fc96ba9430) (KB2506212) (Important) | [Windows Server 2003 Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=0209a004-f23a-40d9-991f-864046f4605f) (Low) | [Windows Server 2003 Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=9fbfc742-6c74-49a2-b3cc-e1d5d8c84b77) (Important) | [Windows Server 2003 Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=af320f27-bb3a-4e76-a279-4632267c8761) (Important) |
| Windows Server 2003 x64 Edition Service Pack 2 | [Internet Explorer 6](http://www.microsoft.com/downloads/details.aspx?familyid=5d8f14d1-85cc-478f-8b50-5c355a331f59) (Moderate) [Internet Explorer 7](http://www.microsoft.com/downloads/details.aspx?familyid=9d8bbea9-c456-4569-ad96-c2cd0f5fae7e) (Moderate) [Internet Explorer 8](http://www.microsoft.com/downloads/details.aspx?familyid=979d2ec5-5114-4ec7-aa97-e9289c590cbb) (Moderate) | [Windows Server 2003 x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=ca0fb4d3-7651-4760-83fa-b71c86cbe459) (Critical) | [Windows Server 2003 x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=ef62db94-4f72-4245-ac9f-6391035e2516) (Critical) | [Windows Server 2003 x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=c8d59f49-45ec-4527-b3a8-4925f710bbfd) (Moderate) | [Microsoft .NET Framework 2.0 Service Pack 2 and Microsoft .NET Framework 3.5 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=ce925e76-cb85-48f6-8c0f-e53fa2b09be6) (KB2446704) (Critical) [Microsoft .NET Framework 4.0](http://www.microsoft.com/downloads/details.aspx?familyid=91aa6772-4811-4a58-9bc0-8aa271ed99df)[1](KB2446708) (Critical) | [Windows Server 2003 x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=d5adaf4e-4cd7-42ea-8202-31b5c856f5e3) (KB2412687) (Critical) | [Windows Server 2003 x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=a0192dbc-4d0d-4555-9ef7-3e10209a6389) (Important) | [JScript 5.6 and VBScript 5.6](http://www.microsoft.com/downloads/details.aspx?familyid=83ce6c99-a57d-4ed1-972b-a6b6798e6675) (KB2510587) (Critical) [JScript 5.7 and VBScript 5.7](http://www.microsoft.com/downloads/details.aspx?familyid=af791715-77a1-405b-a69e-d63f75dd7ccd) (KB2510581) (Critical) [JScript 5.8 and VBScript 5.8](http://www.microsoft.com/downloads/details.aspx?familyid=bf0a2966-25c4-4717-bcd6-016ce610d220) (KB2510531) (Critical) | [Windows Server 2003 x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=3a498ff0-21d9-493a-b127-6bc20f1baf95) (Important) | [Windows Server 2003 x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=f04d939a-da11-4a9f-9e03-b6c3bf3ca58b) (KB2491683) (Important) [Windows Server 2003 x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=12b01f3a-ccf8-41c1-ac5a-e417a6ddbe95) (KB2506212) (Important) | [Windows Server 2003 x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=6c287571-54ea-4298-8b7d-b98b2c830cc3) (Low) | [Windows Server 2003 x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=897b97b0-1bab-4b1b-b417-950fab0d4a65) (Important) | [Windows Server 2003 x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=9c95f81c-9812-4070-88d7-34422c638e42) (Important) |
| Windows Server 2003 with SP2 for Itanium-based Systems | [Internet Explorer 6](http://www.microsoft.com/downloads/details.aspx?familyid=8afe86fc-58b4-4a95-b047-c09138fa4f5e) (Moderate) [Internet Explorer 7](http://www.microsoft.com/downloads/details.aspx?familyid=f1abfb48-3c8a-4b2d-b739-cc61628b387d) (Moderate) | [Windows Server 2003 with SP2 for Itanium-based Systems](http://www.microsoft.com/downloads/details.aspx?familyid=87eb8b93-9829-45ec-9528-52787732044e) (Critical) | [Windows Server 2003 with SP2 for Itanium-based Systems](http://www.microsoft.com/downloads/details.aspx?familyid=79aeb3cd-7c73-467b-b91e-02c6ea01e911) (Critical) | [Windows Server 2003 with SP2 for Itanium-based Systems](http://www.microsoft.com/downloads/details.aspx?familyid=9c784734-f44f-4a3c-8223-6289f7dc2ad8) (No severity rating[1]) | [Microsoft .NET Framework 2.0 Service Pack 2 and Microsoft .NET Framework 3.5 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=ce925e76-cb85-48f6-8c0f-e53fa2b09be6) (KB2446704) (Critical) [Microsoft .NET Framework 4.0](http://www.microsoft.com/downloads/details.aspx?familyid=91aa6772-4811-4a58-9bc0-8aa271ed99df)[1](KB2446708) (Critical) | [Windows Server 2003 with SP2 for Itanium-based Systems](http://www.microsoft.com/downloads/details.aspx?familyid=72a513bb-f901-4992-8562-d1afe1afec8a) (KB2412687) (Critical) | [Windows Server 2003 with SP2 for Itanium-based Systems](http://www.microsoft.com/downloads/details.aspx?familyid=f5ad6963-2d6a-4d59-9e25-4fc088647fcd) (Important) | [JScript 5.6 and VBScript 5.6](http://www.microsoft.com/downloads/details.aspx?familyid=b7d36bae-7ca4-4a40-9efb-13f484fa5518) (KB2510587) (Critical) [JScript 5.7 and VBScript 5.7](http://www.microsoft.com/downloads/details.aspx?familyid=3f519013-ed14-41a8-aa45-cf8b095d3152) (KB2510581) (Critical) | [Windows Server 2003 with SP2 for Itanium-based Systems](http://www.microsoft.com/downloads/details.aspx?familyid=c71f4398-2e3b-4b81-a650-8806e618db7f) (Important) | [Windows Server 2003 with SP2 for Itanium-based Systems](http://www.microsoft.com/downloads/details.aspx?familyid=efb575c7-3259-49b1-b59c-89d9544e37a6) (KB2491683) (Important) [Windows Server 2003 with SP2 for Itanium-based Systems](http://www.microsoft.com/downloads/details.aspx?familyid=03a7ee49-7bd6-4215-9779-1b48c10d08b9) (KB2506212) (Important) | [Windows Server 2003 with SP2 for Itanium-based Systems](http://www.microsoft.com/downloads/details.aspx?familyid=3fb450a0-d087-4f36-9301-05ffbf94cc1a) (Low) | [Windows Server 2003 with SP2 for Itanium-based Systems](http://www.microsoft.com/downloads/details.aspx?familyid=ede38974-4e57-4ea1-8731-b91e96534693) (Important) | [Windows Server 2003 with SP2 for Itanium-based Systems](http://www.microsoft.com/downloads/details.aspx?familyid=f58cf64a-bf31-4496-be75-5775a123338b) (Important) |
| Windows Vista | |||||||||||||
| **Bulletin Identifier** | [**MS11-018**](http://go.microsoft.com/fwlink/?linkid=214126) | [**MS11-019**](http://go.microsoft.com/fwlink/?linkid=212314) | [**MS11-020**](http://go.microsoft.com/fwlink/?linkid=212236) | [**MS11-027**](http://go.microsoft.com/fwlink/?linkid=214005) | [**MS11-028**](http://go.microsoft.com/fwlink/?linkid=207931) | [**MS11-029**](http://go.microsoft.com/fwlink/?linkid=208524) | [**MS11-030**](http://go.microsoft.com/fwlink/?linkid=212595) | [**MS11-031**](http://go.microsoft.com/fwlink/?linkid=212243) | [**MS11-032**](http://go.microsoft.com/fwlink/?linkid=212224) | [**MS11-024**](http://go.microsoft.com/fwlink/?linkid=212226) | [**MS11-026**](http://go.microsoft.com/fwlink/?linkid=212523) | [**MS11-033**](http://go.microsoft.com/fwlink/?linkid=208110) | [**MS11-034**](http://go.microsoft.com/fwlink/?linkid=211826) |
| **Aggregate Severity Rating** | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | None | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) |
| Windows Vista Service Pack 1 and Windows Vista Service Pack 2 | [Internet Explorer 7](http://www.microsoft.com/downloads/details.aspx?familyid=00c3c176-feff-4022-ac4c-2d4732ca3d78) (Critical) [Internet Explorer 8](http://www.microsoft.com/downloads/details.aspx?familyid=5ea94705-4f76-4b0d-bbbc-afb5e75204bf) (Critical) | [Windows Vista Service Pack 1 and Windows Vista Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=da8dd55d-6630-484e-836c-9feeab5cc311) (Critical) | [Windows Vista Service Pack 1 and Windows Vista Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=d6eddff4-a242-4dec-9d84-72891db2b754) (Critical) | [Windows Vista Service Pack 1 and Windows Vista Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=80bf050a-9aff-4cd4-8e2f-196b0a92b1c0) (Critical) | Windows Vista Service Pack 1 only: [Microsoft .NET Framework 2.0 Service Pack 2 and Microsoft .NET Framework 3.5 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=94b6a1b3-e048-437b-a224-2a64b3735bc3) (KB2449741) (Critical) Windows Vista Service Pack 2 only: [Microsoft .NET Framework 2.0 Service Pack 2 and Microsoft .NET Framework 3.5 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=1407aaec-b3e0-404c-b84f-0c8e808614c4) (KB2449742) (Critical) Windows Vista Service Pack 1 and Windows Vista Service Pack 2: [Microsoft .NET Framework 4.0](http://www.microsoft.com/downloads/details.aspx?familyid=91aa6772-4811-4a58-9bc0-8aa271ed99df)[1](KB2446708) (Critical) | [Windows Vista Service Pack 1 and Windows Vista Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=4ff2e440-79c2-4045-b225-913d1740fdb9) (KB2412687) (Critical) | [Windows Vista Service Pack 1 and Windows Vista Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=2a17e44f-54aa-423d-b3c7-a4f404f7c28b) (Critical) | [JScript 5.7 and VBScript 5.7](http://www.microsoft.com/downloads/details.aspx?familyid=719e2c86-30e5-4cd5-94f4-d6de54efee5f) (KB2510581) (Critical) [JScript 5.8 and VBScript 5.8](http://www.microsoft.com/downloads/details.aspx?familyid=21decb84-75ef-4bde-a802-1e661a505e94)[1](KB2510531) (Critical) | [Windows Vista Service Pack 1 and Windows Vista Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=e7c4fc81-d1ef-4378-862b-e955d75fb2de) (Critical) | [Windows Vista Service Pack 1 and Windows Vista Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=11a8f240-51b3-4e31-a24a-a235179f3396) (KB2491683) (Important) [Windows Vista Service Pack 1 and Windows Vista Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=e6cba040-9d7c-4777-a2f7-e4dd11dfb845) (KB2506212) (Important) | [Windows Vista Service Pack 1 and Windows Vista Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=c8fce0fb-4c90-479b-8ce9-75e60d52d256) (Important) | Not applicable | [Windows Vista Service Pack 1 and Windows Vista Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=b4743167-9614-445a-9e91-10efdac505a8) (Important) |
| Windows Vista x64 Edition Service Pack 1 and Windows Vista x64 Edition Service Pack 2 | [Internet Explorer 7](http://www.microsoft.com/downloads/details.aspx?familyid=79f52733-44e4-47b6-86ca-1395a095b4e7) (Critical) [Internet Explorer 8](http://www.microsoft.com/downloads/details.aspx?familyid=bc63b233-9db0-4fb1-a61c-fa7e9e44ba10) (Critical) | [Windows Vista x64 Edition Service Pack 1 and Windows Vista x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=040f8b46-f458-4a72-a1b0-ad8a65a1194c) (Critical) | [Windows Vista x64 Edition Service Pack 1 and Windows Vista x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=2878c587-6544-40b4-9288-fc3b3ce1128d) (Critical) | [Windows Vista x64 Edition Service Pack 1 and Windows Vista x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=a81412d0-2516-4bf4-87f7-3e41ebf6b82b) (Critical) | Windows Vista x64 Edition Service Pack 1 only: [Microsoft .NET Framework 2.0 Service Pack 2 and Microsoft .NET Framework 3.5 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=94b6a1b3-e048-437b-a224-2a64b3735bc3) (KB2449741) (Critical) Windows Vista x64 Edition Service Pack 2 only: [Microsoft .NET Framework 2.0 Service Pack 2 and Microsoft .NET Framework 3.5 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=1407aaec-b3e0-404c-b84f-0c8e808614c4) (KB2449742) (Critical) Windows Vista x64 Edition Service Pack 1 and Windows Vista x64 Edition Service Pack 2: [Microsoft .NET Framework 4.0](http://www.microsoft.com/downloads/details.aspx?familyid=91aa6772-4811-4a58-9bc0-8aa271ed99df)[1](KB2446708) (Critical) | [Windows Vista x64 Edition Service Pack 1 and Windows Vista x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=4d826026-e62a-4cec-8682-49fbe7f65cd6) (KB2412687) (Critical) | [Windows Vista x64 Edition Service Pack 1 and Windows Vista x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=e708d24f-e348-4c4d-99ed-e78dd1689d01) (Critical) | [JScript 5.7 and VBScript 5.7](http://www.microsoft.com/downloads/details.aspx?familyid=89b9d01e-bcbc-4f2c-973b-51051494f406) (KB2510581) (Critical) [JScript 5.8 and VBScript 5.8](http://www.microsoft.com/downloads/details.aspx?familyid=d4ac199e-7bf8-4661-a4e5-c53719b2673a)[1](KB2510531) (Critical) | [Windows Vista x64 Edition Service Pack 1 and Windows Vista x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=8d654a78-0e4f-452c-8874-fbf478813857) (Critical) | [Windows Vista x64 Edition Service Pack 1 and Windows Vista x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=61db662e-88d7-4454-b4b7-e987728fb137) (KB2491683) (Important) [Windows Vista x64 Edition Service Pack 1 and Windows Vista x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=1c942282-0f80-46c1-aeef-1ef948e105a3) (KB2506212) (Important) | [Windows Vista x64 Edition Service Pack 1 and Windows Vista x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=7da10b64-d0a9-4e42-aa3a-87c657122a8c) (Important) | Not applicable | [Windows Vista x64 Edition Service Pack 1 and Windows Vista x64 Edition Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=7e410d5c-b9f7-4a63-8300-36b2d57c6128) (Important) |
| Windows Server 2008 | |||||||||||||
| **Bulletin Identifier** | [**MS11-018**](http://go.microsoft.com/fwlink/?linkid=214126) | [**MS11-019**](http://go.microsoft.com/fwlink/?linkid=212314) | [**MS11-020**](http://go.microsoft.com/fwlink/?linkid=212236) | [**MS11-027**](http://go.microsoft.com/fwlink/?linkid=214005) | [**MS11-028**](http://go.microsoft.com/fwlink/?linkid=207931) | [**MS11-029**](http://go.microsoft.com/fwlink/?linkid=208524) | [**MS11-030**](http://go.microsoft.com/fwlink/?linkid=212595) | [**MS11-031**](http://go.microsoft.com/fwlink/?linkid=212243) | [**MS11-032**](http://go.microsoft.com/fwlink/?linkid=212224) | [**MS11-024**](http://go.microsoft.com/fwlink/?linkid=212226) | [**MS11-026**](http://go.microsoft.com/fwlink/?linkid=212523) | [**MS11-033**](http://go.microsoft.com/fwlink/?linkid=208110) | [**MS11-034**](http://go.microsoft.com/fwlink/?linkid=211826) |
| **Aggregate Severity Rating** | [**Moderate**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Moderate**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Low**](http://go.microsoft.com/fwlink/?linkid=21140) | None | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) |
| Windows Server 2008 for 32-bit Systems and Windows Server 2008 for 32-bit Systems Service Pack 2 | [Internet Explorer 7](http://www.microsoft.com/downloads/details.aspx?familyid=7d8603b8-bb52-4cf6-be8b-bb3475d30fc5)** (Moderate) [Internet Explorer 8](http://www.microsoft.com/downloads/details.aspx?familyid=d5d76e90-1cef-47e8-9d8d-2c5a43f42ba3)** (Moderate) | [Windows Server 2008 for 32-bit Systems and Windows Server 2008 for 32-bit Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=f8c9390a-5ca1-492a-9e35-a516de48deb5)* (Critical) | [Windows Server 2008 for 32-bit Systems and Windows Server 2008 for 32-bit Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=31c48ba9-7774-4633-862d-5c27c3703584)* (Critical) | [Windows Server 2008 for 32-bit Systems and Windows Server 2008 for 32-bit Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=c3247886-76d0-4292-be9d-3e9b0221c46a)** (Moderate) | Windows Server 2008 for 32-bit Systems only: [Microsoft .NET Framework 2.0 Service Pack 2 and Microsoft .NET Framework 3.5 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=94b6a1b3-e048-437b-a224-2a64b3735bc3)** (KB2449741) (Critical) Windows Server 2008 for 32-bit Systems Service Pack 2 only: [Microsoft .NET Framework 2.0 Service Pack 2 and Microsoft .NET Framework 3.5 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=1407aaec-b3e0-404c-b84f-0c8e808614c4)** (KB2449742) (Critical) Windows Server 2008 for 32-bit Systems and Windows Server 2008 for 32-bit Systems Service Pack 2: [Microsoft .NET Framework 4.0](http://www.microsoft.com/downloads/details.aspx?familyid=91aa6772-4811-4a58-9bc0-8aa271ed99df)**[1](KB2446708) (Critical) | [Windows Server 2008 for 32-bit Systems and Windows Server 2008 for 32-bit Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=fbada866-7d36-4b85-acde-fd856a998737)*** (KB2412687) (Critical) | [Windows Server 2008 for 32-bit Systems and Windows Server 2008 for 32-bit Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=9894be38-a582-4c15-ad0e-cc3afab2aebc)* (Critical) | [JScript 5.7 and VBScript 5.7](http://www.microsoft.com/downloads/details.aspx?familyid=d8b33ffd-eff1-4a10-b6fc-3c8f01e0fec5)** (KB2510581) (Critical) [JScript 5.8 and VBScript 5.8](http://www.microsoft.com/downloads/details.aspx?familyid=afd128ff-717f-4d98-b214-f2c28d59623d)**[1](KB2510531) (Critical) | [Windows Server 2008 for 32-bit Systems and Windows Server 2008 for 32-bit Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=9105377e-83c7-4010-8fd6-26e42e98c2cc)* (Critical) | [Windows Server 2008 for 32-bit Systems and Windows Server 2008 for 32-bit Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=90f56368-776b-4d45-ad68-91afbd316d25)** (KB2491683) (Important) [Windows Server 2008 for 32-bit Systems and Windows Server 2008 for 32-bit Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=fa972742-1166-4a9e-ab64-6a4f968f9c6d)* (KB2506212) (Important) | [Windows Server 2008 for 32-bit Systems and Windows Server 2008 for 32-bit Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=036f1285-7484-4e3b-8799-2c6c08166596)** (Low) | Not applicable | [Windows Server 2008 for 32-bit Systems and Windows Server 2008 for 32-bit Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=c6ac26b8-8cc8-40fe-baab-22bf13df1aa8)* (Important) |
| Windows Server 2008 for x64-based Systems and Windows Server 2008 for x64-based Systems Service Pack 2 | [Internet Explorer 7](http://www.microsoft.com/downloads/details.aspx?familyid=c6d58f64-bdd5-4fe6-96f4-9641b8e7b570)** (Moderate) [Internet Explorer 8](http://www.microsoft.com/downloads/details.aspx?familyid=51203a31-368b-4b47-96a5-9e9e5a55cd76)** (Moderate) | [Windows Server 2008 for x64-based Systems and Windows Server 2008 for x64-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=b0cfd5e0-6de5-4863-b5e4-b223a0e36d72)* (Critical) | [Windows Server 2008 for x64-based Systems and Windows Server 2008 for x64-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=de843115-cf98-4511-aa93-f620e4572555)* (Critical) | [Windows Server 2008 for x64-based Systems and Windows Server 2008 for x64-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=51521b6b-94a7-4bcf-ad5f-fc304728b10f)** (Moderate) | Windows Server 2008 for x64-based Systems only: [Microsoft .NET Framework 2.0 Service Pack 2 and Microsoft .NET Framework 3.5 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=94b6a1b3-e048-437b-a224-2a64b3735bc3)** (KB2449741) (Critical) Windows Server 2008 for x64-based Systems Service Pack 2 only: [Microsoft .NET Framework 2.0 Service Pack 2 and Microsoft .NET Framework 3.5 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=1407aaec-b3e0-404c-b84f-0c8e808614c4)** (KB2449742) (Critical) Windows Server 2008 for x64-based Systems and Windows Server 2008 for x64-based Systems Service Pack 2: [Microsoft .NET Framework 4.0](http://www.microsoft.com/downloads/details.aspx?familyid=91aa6772-4811-4a58-9bc0-8aa271ed99df)**[1](KB2446708) (Critical) | [Windows Server 2008 for x64-based Systems and Windows Server 2008 for x64-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=8f4ddfcb-374d-4cad-8c61-2b988b46f628)*** (KB2412687) (Critical) | [Windows Server 2008 for x64-based Systems and Windows Server 2008 for x64-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=2d7d2021-020f-4cc9-a027-258d7e5faec9)* (Critical) | [JScript 5.7 and VBScript 5.7](http://www.microsoft.com/downloads/details.aspx?familyid=6c2e6b87-afcd-461a-8a43-9a2fb277b18a)** (KB2510581) (Critical) [JScript 5.8 and VBScript 5.8](http://www.microsoft.com/downloads/details.aspx?familyid=40e8beca-0b5a-43b0-98f8-b32a82ad65d6)**[1](KB2510531) (Critical) | [Windows Server 2008 for x64-based Systems and Windows Server 2008 for x64-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=060e8b20-edca-4427-9d60-eb57261eb668)* (Critical) | [Windows Server 2008 for x64-based Systems and Windows Server 2008 for x64-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=22a001fc-5c2e-4539-85c9-0c2054a1777d)** (KB2491683) (Important) [Windows Server 2008 for x64-based Systems and Windows Server 2008 for x64-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=fc250c8a-ebaf-4264-9393-dc23cc372d9f)* (KB2506212) (Important) | [Windows Server 2008 for x64-based Systems and Windows Server 2008 for x64-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=1438cec8-8dab-4510-ad75-dc6959dac0d8)** (Low) | Not applicable | [Windows Server 2008 for x64-based Systems and Windows Server 2008 for x64-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=ac49f5d3-5e2f-4916-99be-a3254278da7e)* (Important) |
| Windows Server 2008 for Itanium-based Systems and Windows Server 2008 for Itanium-based Systems Service Pack 2 | [Internet Explorer 7](http://www.microsoft.com/downloads/details.aspx?familyid=f6f6f22c-fc7f-4e96-b6b5-be3c1acecf6e) (Moderate) | [Windows Server 2008 for Itanium-based Systems and Windows Server 2008 for Itanium-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=8eaf51cd-2f6e-4bbc-bc4f-9deed03649ac) (Critical) | [Windows Server 2008 for Itanium-based Systems and Windows Server 2008 for Itanium-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=b89b8e28-cd98-4bcc-8729-5e51d52d1e92) (Critical) | [Windows Server 2008 for Itanium-based Systems and Windows Server 2008 for Itanium-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=e7c38b0d-7240-420a-88d3-2749a40e386f) (No severity rating[1]) | Windows Server 2008 for Itanium-based Systems only: [Microsoft .NET Framework 2.0 Service Pack 2 and Microsoft .NET Framework 3.5 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=94b6a1b3-e048-437b-a224-2a64b3735bc3) (KB2449741) (Critical) Windows Server 2008 for Itanium-based Systems Service Pack 2 only: [Microsoft .NET Framework 2.0 Service Pack 2 and Microsoft .NET Framework 3.5 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=1407aaec-b3e0-404c-b84f-0c8e808614c4) (KB2449742) (Critical) Windows Server 2008 for Itanium-based Systems and Windows Server 2008 for Itanium-based Systems Service Pack 2: [Microsoft .NET Framework 4.0](http://www.microsoft.com/downloads/details.aspx?familyid=91aa6772-4811-4a58-9bc0-8aa271ed99df)[1](KB2446708) (Critical) | [Windows Server 2008 for Itanium-based Systems and Windows Server 2008 for Itanium-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=2fd71543-0e18-4907-89b9-355d24d7db69) (KB2412687) (Critical) | [Windows Server 2008 for Itanium-based Systems and Windows Server 2008 for Itanium-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=c0275df0-10ac-4500-ab86-b7e9a34f8e1d) (Critical) | [JScript 5.7 and VBScript 5.7](http://www.microsoft.com/downloads/details.aspx?familyid=afb49d24-1913-4e5f-a3ea-c6c9642e2017) (KB2510581) (Critical) | [Windows Server 2008 for Itanium-based Systems and Windows Server 2008 for Itanium-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=2b8571cb-2dae-4bff-9f13-feb89840044c) (Critical) | [Windows Server 2008 for Itanium-based Systems and Windows Server 2008 for Itanium-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=421024f1-aa86-459e-b6de-53851a3fcba2) (KB2506212) (Important) | [Windows Server 2008 for Itanium-based Systems and Windows Server 2008 for Itanium-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=f35ecdd1-6b5c-40e7-a00b-ca083bdf5cba) (Low) | Not applicable | [Windows Server 2008 for Itanium-based Systems and Windows Server 2008 for Itanium-based Systems Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=3b93de4f-01f4-4efd-afc1-31d87b92fad2) (Important) |
| Windows 7 | |||||||||||||
| **Bulletin Identifier** | [**MS11-018**](http://go.microsoft.com/fwlink/?linkid=214126) | [**MS11-019**](http://go.microsoft.com/fwlink/?linkid=212314) | [**MS11-020**](http://go.microsoft.com/fwlink/?linkid=212236) | [**MS11-027**](http://go.microsoft.com/fwlink/?linkid=214005) | [**MS11-028**](http://go.microsoft.com/fwlink/?linkid=207931) | [**MS11-029**](http://go.microsoft.com/fwlink/?linkid=208524) | [**MS11-030**](http://go.microsoft.com/fwlink/?linkid=212595) | [**MS11-031**](http://go.microsoft.com/fwlink/?linkid=212243) | [**MS11-032**](http://go.microsoft.com/fwlink/?linkid=212224) | [**MS11-024**](http://go.microsoft.com/fwlink/?linkid=212226) | [**MS11-026**](http://go.microsoft.com/fwlink/?linkid=212523) | [**MS11-033**](http://go.microsoft.com/fwlink/?linkid=208110) | [**MS11-034**](http://go.microsoft.com/fwlink/?linkid=211826) |
| **Aggregate Severity Rating** | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | None | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | None | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) |
| Windows 7 for 32-bit Systems and Windows 7 for 32-bit Systems Service Pack 1 | [Internet Explorer 8](http://www.microsoft.com/downloads/details.aspx?familyid=59676b71-8b9d-4230-a9e0-b20db3e3ec7e) (Critical) | [Windows 7 for 32-bit Systems and Windows 7 for 32-bit Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=0dcba089-19f7-46ca-9e52-24eaebad4715) (Critical) | [Windows 7 for 32-bit Systems and Windows 7 for 32-bit Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=d3ef905b-3584-4842-9ec2-cf3856305d49) (Critical) | [Windows 7 for 32-bit Systems and Windows 7 for 32-bit Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=46510959-e4a2-4c21-b33c-fd3d97b3ac3d) (Critical) | Windows 7 for 32-bit Systems only: [Microsoft .NET Framework 3.5.1](http://www.microsoft.com/downloads/details.aspx?familyid=157aa425-953c-4fc9-ab76-4e65d4be8baa) (KB2446709) (Critical) Windows 7 for 32-bit Systems Service Pack 1 only: [Microsoft .NET Framework 3.5.1](http://www.microsoft.com/downloads/details.aspx?familyid=8f87b8aa-1a2a-405e-aee0-9247d553756a) (KB2446710) (Critical) Windows 7 for 32-bit Systems and Windows 7 for 32-bit Systems Service Pack 1: [Microsoft .NET Framework 4.0](http://www.microsoft.com/downloads/details.aspx?familyid=91aa6772-4811-4a58-9bc0-8aa271ed99df)[1](KB2446708) (Critical) | Not applicable | [Windows 7 for 32-bit Systems and Windows 7 for 32-bit Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=8fdae09b-d1bb-4ef5-aa45-2a05f2a5e12d) (Critical) | [JScript 5.8 and VBScript 5.8](http://www.microsoft.com/downloads/details.aspx?familyid=17ebf291-fdae-4e78-9377-871b3103ce16)[1](KB2510531) (Critical) | [Windows 7 for 32-bit Systems and Windows 7 for 32-bit Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=751c45ea-0943-4948-807f-8716c6ff9198) (Critical) | [Windows 7 for 32-bit Systems and Windows 7 for 32-bit Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=bf762b86-b949-4e84-8ca4-93ebe669c1b8) (KB2491683) (Important) [Windows 7 for 32-bit Systems and Windows 7 for 32-bit Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=0f5a122e-dd5e-4b08-881a-f13b38642720) (KB2506212) (Important) | [Windows 7 for 32-bit Systems and Windows 7 for 32-bit Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=aed201c1-f1fb-4df9-8875-6f57ea0eb15b) (Important) | Not applicable | [Windows 7 for 32-bit Systems and Windows 7 for 32-bit Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=6e7ff003-ff3f-49bb-8e45-d869885dd8d7) (Important) |
| Windows 7 for x64-based Systems and Windows 7 for x64-based Systems Service Pack 1 | [Internet Explorer 8](http://www.microsoft.com/downloads/details.aspx?familyid=3a998678-2678-489e-8711-39322663147d) (Critical) | [Windows 7 for x64-based Systems and Windows 7 for x64-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=b7fd356a-56d0-4638-8901-40acfa600f25) (Critical) | [Windows 7 for x64-based Systems and Windows 7 for x64-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=7ddc943b-6868-4e8f-a869-89b47133c287) (Critical) | [Windows 7 for x64-based Systems and Windows 7 for x64-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=432555cf-aed8-4329-a74f-526441521082) (Critical) | Windows 7 for x64-based Systems only: [Microsoft .NET Framework 3.5.1](http://www.microsoft.com/downloads/details.aspx?familyid=157aa425-953c-4fc9-ab76-4e65d4be8baa) (KB2446709) (Critical) Windows 7 for x64-based Systems Service Pack 1 only: [Microsoft .NET Framework 3.5.1](http://www.microsoft.com/downloads/details.aspx?familyid=8f87b8aa-1a2a-405e-aee0-9247d553756a) (KB2446710) (Critical) Windows 7 for x64-based Systems and Windows 7 for x64-based Systems Service Pack 1: [Microsoft .NET Framework 4.0](http://www.microsoft.com/downloads/details.aspx?familyid=91aa6772-4811-4a58-9bc0-8aa271ed99df)[1](KB2446708) (Critical) | Not applicable | [Windows 7 for x64-based Systems and Windows 7 for x64-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=40879dfb-efa4-41ba-8d5c-22e926a55eef) (Critical) | [JScript 5.8 and VBScript 5.8](http://www.microsoft.com/downloads/details.aspx?familyid=c95ad86d-da58-4d7a-9ffd-8441f92baaa5)[1](KB2510531) (Critical) | [Windows 7 for x64-based Systems and Windows 7 for x64-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=976c882a-bc07-4128-927f-82a2df46cf45) (Critical) | [Windows 7 for x64-based Systems and Windows 7 for x64-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=a6793ecf-a3f6-4989-8e4c-c5c0005f9ac4) (KB2491683) (Important) [Windows 7 for x64-based Systems and Windows 7 for x64-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=658301f1-103a-48a2-9b67-61cf8e1dad50) (KB2506212) (Important) | [Windows 7 for x64-based Systems and Windows 7 for x64-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=1a32bf04-7eed-4d27-a8e4-054b4a5b76cb) (Important) | Not applicable | [Windows 7 for x64-based Systems and Windows 7 for x64-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=0c0aef7e-501c-4ca3-ae7f-497a8c169121) (Important) |
| Windows Server 2008 R2 | |||||||||||||
| **Bulletin Identifier** | [**MS11-018**](http://go.microsoft.com/fwlink/?linkid=214126) | [**MS11-019**](http://go.microsoft.com/fwlink/?linkid=212314) | [**MS11-020**](http://go.microsoft.com/fwlink/?linkid=212236) | [**MS11-027**](http://go.microsoft.com/fwlink/?linkid=214005) | [**MS11-028**](http://go.microsoft.com/fwlink/?linkid=207931) | [**MS11-029**](http://go.microsoft.com/fwlink/?linkid=208524) | [**MS11-030**](http://go.microsoft.com/fwlink/?linkid=212595) | [**MS11-031**](http://go.microsoft.com/fwlink/?linkid=212243) | [**MS11-032**](http://go.microsoft.com/fwlink/?linkid=212224) | [**MS11-024**](http://go.microsoft.com/fwlink/?linkid=212226) | [**MS11-026**](http://go.microsoft.com/fwlink/?linkid=212523) | [**MS11-033**](http://go.microsoft.com/fwlink/?linkid=208110) | [**MS11-034**](http://go.microsoft.com/fwlink/?linkid=211826) |
| **Aggregate Severity Rating** | [**Moderate**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Moderate**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | None | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Critical**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Low**](http://go.microsoft.com/fwlink/?linkid=21140) | None | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) |
| Windows Server 2008 R2 for x64-based Systems and Windows Server 2008 R2 for x64-based Systems Service Pack 1 | [Internet Explorer 8](http://www.microsoft.com/downloads/details.aspx?familyid=c7b2482b-44bf-4c01-99d8-f93868659a24)** (Moderate) | [Windows Server 2008 R2 for x64-based Systems and Windows Server 2008 R2 for x64-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=27a3847b-695b-4f60-aea5-86b0dbe68945)* (Critical) | [Windows Server 2008 R2 for x64-based Systems and Windows Server 2008 R2 for x64-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=c4352802-9c5a-4c07-8303-3a4b78d3f954)* (Critical) | [Windows Server 2008 R2 for x64-based Systems and Windows Server 2008 R2 for x64-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=e4fa8ed0-acb0-4864-be18-29a27f8501de)** (Moderate) | Windows Server 2008 R2 for x64-based Systems only: [Microsoft .NET Framework 3.5.1](http://www.microsoft.com/downloads/details.aspx?familyid=157aa425-953c-4fc9-ab76-4e65d4be8baa)* (KB2446709) (Critical) Windows Server 2008 R2 for x64-based Systems only: [Microsoft .NET Framework 4.0](http://www.microsoft.com/downloads/details.aspx?familyid=91aa6772-4811-4a58-9bc0-8aa271ed99df)[1](KB2446708) (Critical) Windows Server 2008 R2 for x64-based Systems Service Pack 1 only: [Microsoft .NET Framework 3.5.1](http://www.microsoft.com/downloads/details.aspx?familyid=8f87b8aa-1a2a-405e-aee0-9247d553756a)* (KB2446710) (Critical) Windows Server 2008 R2 for x64-based Systems Service Pack 1 only: [Microsoft .NET Framework 4.0](http://www.microsoft.com/downloads/details.aspx?familyid=91aa6772-4811-4a58-9bc0-8aa271ed99df)*[1](KB2446708) (Critical) | Not applicable | [Windows Server 2008 R2 for x64-based Systems and Windows Server 2008 R2 for x64-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=2084c726-187e-41f9-9bea-da18f490d29e)* (Critical) | [JScript 5.8 and VBScript 5.8](http://www.microsoft.com/downloads/details.aspx?familyid=aecc2c7a-285c-409d-be23-c5b4b5449496)**[1](KB2510531) (Critical) | [Windows Server 2008 R2 for x64-based Systems and Windows Server 2008 R2 for x64-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=6f2a52cc-4833-448d-becc-2eac1a447410)* (Critical) | [Windows Server 2008 R2 for x64-based Systems and Windows Server 2008 R2 for x64-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=465c0478-6a74-4b00-8608-938cc492549f)** (KB2491683) (Important) [Windows Server 2008 R2 for x64-based Systems and Windows Server 2008 R2 for x64-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=4c5c3a0f-0672-49d0-bcbd-c7f40e11d092)* (KB2506212) (Important) | [Windows Server 2008 R2 for x64-based Systems and Windows Server 2008 R2 for x64-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=665faa7e-2368-4421-9dd5-ea6df2c79498)** (Low) | Not applicable | [Windows Server 2008 R2 for x64-based Systems and Windows Server 2008 R2 for x64-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=2fc66224-45c6-4e8f-ad00-6a1ec30b4505)* (Important) |
| Windows Server 2008 R2 for Itanium-based Systems and Windows Server 2008 R2 for Itanium-based Systems Service Pack 1 | [Internet Explorer 8](http://www.microsoft.com/downloads/details.aspx?familyid=af6db318-fbec-4286-a3a7-4081620146e5) (Moderate) | [Windows Server 2008 R2 for Itanium-based Systems and Windows Server 2008 R2 for Itanium-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=1e7d3f21-bdbd-4826-855d-85422aa5f836) (Critical) | [Windows Server 2008 R2 for Itanium-based Systems and Windows Server 2008 R2 for Itanium-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=0005377b-443f-44ca-a890-620b2dcea6f1) (Critical) | [Windows Server 2008 R2 for Itanium-based Systems and Windows Server 2008 R2 for Itanium-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=d7bcf4d7-b697-4c5f-adbc-a2b3700e0ad5) (Moderate) | Windows Server 2008 R2 for Itanium-based Systems only: [Microsoft .NET Framework 3.5.1](http://www.microsoft.com/downloads/details.aspx?familyid=157aa425-953c-4fc9-ab76-4e65d4be8baa) (KB2446709) (Critical) Windows Server 2008 R2 for Itanium-based Systems Service Pack 1 only: [Microsoft .NET Framework 3.5.1](http://www.microsoft.com/downloads/details.aspx?familyid=8f87b8aa-1a2a-405e-aee0-9247d553756a) (KB2446710) (Critical) Windows Server 2008 R2 for Itanium-based Systems and Windows Server 2008 R2 for Itanium-based Systems Service Pack 1: [Microsoft .NET Framework 4.0](http://www.microsoft.com/downloads/details.aspx?familyid=91aa6772-4811-4a58-9bc0-8aa271ed99df)[1](KB2446708) (Critical) | Not applicable | [Windows Server 2008 R2 for Itanium-based Systems and Windows Server 2008 R2 for Itanium-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=34d2793e-a2cd-49f6-b524-6598ea86175f) (Critical) | [JScript 5.8 and VBScript 5.8](http://www.microsoft.com/downloads/details.aspx?familyid=e1bc0ed8-5a93-4d01-b407-919dfd894b5f)[1](KB2510531) (Critical) | [Windows Server 2008 R2 for Itanium-based Systems and Windows Server 2008 R2 for Itanium-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=c6ca0b7c-8151-4d54-aa9b-5ec2b75d8ab6) (Critical) | [Windows Server 2008 R2 for Itanium-based Systems and Windows Server 2008 R2 for Itanium-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=1a993f8c-d28a-4a95-a3c6-059f06e75461) (KB2506212) (Important) | [Windows Server 2008 R2 for Itanium-based Systems and Windows Server 2008 R2 for Itanium-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=140ea384-2877-401f-ac3b-f84f6966e970) (Low) | Not applicable | [Windows Server 2008 R2 for Itanium-based Systems and Windows Server 2008 R2 for Itanium-based Systems Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=485ccf96-27a0-499e-9f52-2836b73d26d2) (Important) |
Notes for Windows Server 2008 and Windows Server 2008 R2
*Server Core installation affected. This update applies, with the same severity rating, to supported editions of Windows Server 2008 or Windows Server 2008 R2 as indicated, whether or not installed using the Server Core installation option. For more information on this installation option, see the TechNet articles, Managing a Server Core Installation and Servicing a Server Core Installation. Note that the Server Core installation option does not apply to certain editions of Windows Server 2008 and Windows Server 2008 R2; see Compare Server Core Installation Options.
**Server Core installation not affected. The vulnerabilities addressed by this update do not affect supported editions of Windows Server 2008 or Windows Server 2008 R2 as indicated, when installed using the Server Core installation option. For more information on this installation option, see the TechNet articles, Managing a Server Core Installation and Servicing a Server Core Installation. Note that the Server Core installation option does not apply to certain editions of Windows Server 2008 and Windows Server 2008 R2; see Compare Server Core Installation Options.
***Server Core installation not affected. The vulnerabilities addressed by this update do not affect supported editions of Windows Server 2008 or Windows Server 2008 R2 as indicated, when installed using the Server Core installation option, even though files affected by this vulnerability may be present on the system. However, users with the affected files will still be offered this update because the update files are newer (with higher version numbers) than the files that are currently on your system. For more information on this installation option, see the TechNet articles, Managing a Server Core Installation and Servicing a Server Core Installation. Note that the Server Core installation option does not apply to certain editions of Windows Server 2008 and Windows Server 2008 R2; see Compare Server Core Installation Options.
Note for MS11-027
[1]This specific operating system is not affected by the vulnerabilities described in this bulletin. The available update sets the kill bits for third-party controls.
Note for MS11-028
[1].NET Framework 4.0 and .NET Framework 4.0 Client Profile affected. The .NET Framework version 4 redistributable packages are available in two profiles: .NET Framework 4.0 and .NET Framework 4.0 Client Profile. .NET Framework 4.0 Client Profile is a subset of .NET Framework 4.0. The vulnerability addressed in this update affects both .NET Framework 4.0 and .NET Framework 4.0 Client Profile. For more information, see: Installing the .NET Framework.
Note for MS11-029
See also other software categories under this section, Affected Software and Download Locations, for more update files under the same bulletin identifier. This bulletin spans more than one software category.
Note for MS11-031
[1]Systems with Internet Explorer 9 installed are not affected and do not require this update. Systems that have not been upgraded with Internet Explorer 9 will need the correct update for the versions of JScript and VBScript installed on them. For instructions on how to determine the versions of JScript and VBScript installed on your system, see the bulletin.
Note for MS11-024
Where two updates are available for the same operating system, install both updates.
Microsoft Office Suites and Software
| Microsoft Office Suites and Components | ||||
|---|---|---|---|---|
| **Bulletin Identifier** | [**MS11-029**](http://go.microsoft.com/fwlink/?linkid=208524) | [**MS11-021**](http://go.microsoft.com/fwlink/?linkid=210121) | [**MS11-022**](http://go.microsoft.com/fwlink/?linkid=210727) | [**MS11-023**](http://go.microsoft.com/fwlink/?linkid=210206) |
| **Aggregate Severity Rating** | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) |
| Microsoft Office XP Service Pack 3 | [Microsoft Office XP Service Pack 3](http://www.microsoft.com/downloads/details.aspx?familyid=6c87c2a9-3705-4680-8a9b-63b6ec83674d) (KB2509461) (Important) | [Microsoft Excel 2002 Service Pack 3](http://www.microsoft.com/downloads/details.aspx?familyid=db2c5cfe-588c-4646-b86a-3fb8248f7af4) (KB2466169) (Important) | [Microsoft PowerPoint 2002 Service Pack 3](http://www.microsoft.com/downloads/details.aspx?familyid=0d215ab6-c9be-4f43-9501-658bb7ef008e) (KB2464617) (Important) | [Microsoft Office XP Service Pack 3](http://www.microsoft.com/downloads/details.aspx?familyid=6c87c2a9-3705-4680-8a9b-63b6ec83674d) (KB2509461) (Important) |
| Microsoft Office 2003 Service Pack 3 | Not applicable | [Microsoft Excel 2003 Service Pack 3](http://www.microsoft.com/downloads/details.aspx?familyid=916a076d-d754-4092-b23d-c8826db7e397) (KB2502786) (Important) | [Microsoft PowerPoint 2003 Service Pack 3](http://www.microsoft.com/downloads/details.aspx?familyid=2ce8349f-79b1-41ef-a1c0-cbe40ccf9f20) (KB2464588) (Important) | [Microsoft Office 2003 Service Pack 3](http://www.microsoft.com/downloads/details.aspx?familyid=8b68cf68-1606-4649-b860-a64702c6cf33) (KB2509503) (Important) |
| Microsoft Office 2007 Service Pack 2 | Not applicable | [Microsoft Excel 2007 Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=5ae34fe0-03bd-48a9-a7ac-de8f7b1aff90)[1](KB2464583) (Important) | [Microsoft PowerPoint 2007 Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=6b2526fe-a061-4a17-992e-ac867bef130e) (KB2464594) (Important) | [Microsoft Office 2007 Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=dbba0cd4-ab72-4e2b-9524-fd6be27f0b02) (KB2509488) (Important) |
| Microsoft Office 2010 (32-bit editions) | Not applicable | [Microsoft Excel 2010 (32-bit editions)](http://www.microsoft.com/downloads/details.aspx?familyid=a427f0e2-b74d-4ef3-bec4-0a101d09bfa3) (KB2466146) (Important) | [Microsoft PowerPoint 2010 (32-bit editions)](http://www.microsoft.com/downloads/details.aspx?familyid=549ca7f0-44bf-4965-a9d2-aa5e8dac2238) (KB2519975) (Important) | Not applicable |
| Microsoft Office 2010 (64-bit editions) | Not applicable | [Microsoft Excel 2010 (64-bit editions)](http://www.microsoft.com/downloads/details.aspx?familyid=13dca35d-2209-4c5c-9150-d6db2bb3b496) (KB2466146) (Important) | [Microsoft PowerPoint 2010 (64-bit editions)](http://www.microsoft.com/downloads/details.aspx?familyid=ef62deae-2b07-41c9-a4bf-b746566e59ee) (KB2519975) (Important) | Not applicable |
| Microsoft Office for Mac | ||||
| **Bulletin Identifier** | [**MS11-029**](http://go.microsoft.com/fwlink/?linkid=208524) | [**MS11-021**](http://go.microsoft.com/fwlink/?linkid=210121) | [**MS11-022**](http://go.microsoft.com/fwlink/?linkid=210727) | [**MS11-023**](http://go.microsoft.com/fwlink/?linkid=210206) |
| **Aggregate Severity Rating** | None | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) |
| Microsoft Office 2004 for Mac | Not applicable | [Microsoft Office 2004 for Mac](http://www.microsoft.com/downloads/details.aspx?familyid=f756d836-6ab2-4adb-9dee-6cb523d7c1f5) (KB2505924) (Important) | [Microsoft Office 2004 for Mac](http://www.microsoft.com/downloads/details.aspx?familyid=f756d836-6ab2-4adb-9dee-6cb523d7c1f5) (KB2505924) (Important) | [Microsoft Office 2004 for Mac](http://www.microsoft.com/downloads/details.aspx?familyid=f756d836-6ab2-4adb-9dee-6cb523d7c1f5) (KB2505924) (Important) |
| Microsoft Office 2008 for Mac | Not applicable | [Microsoft Office 2008 for Mac](http://www.microsoft.com/downloads/details.aspx?familyid=84dfe3f4-a2a1-47b9-8da1-29ae67230918) (KB2505927) (Important) | [Microsoft Office 2008 for Mac](http://www.microsoft.com/downloads/details.aspx?familyid=84dfe3f4-a2a1-47b9-8da1-29ae67230918) (KB2505927) (Important) | [Microsoft Office 2008 for Mac](http://www.microsoft.com/downloads/details.aspx?familyid=84dfe3f4-a2a1-47b9-8da1-29ae67230918) (KB2505927) (Important) |
| Microsoft Office for Mac 2011 | Not applicable | [Microsoft Office for Mac 2011](http://www.microsoft.com/downloads/details.aspx?familyid=ef1e612f-d8e3-4628-9fe4-ad136f0debd3) (KB2525412) (Important) | [Microsoft Office for Mac 2011](http://www.microsoft.com/downloads/details.aspx?familyid=ef1e612f-d8e3-4628-9fe4-ad136f0debd3) (KB2525412) (Important) | Not applicable |
| Open XML File Format Converter for Mac | Not applicable | [Open XML File Format Converter for Mac](http://www.microsoft.com/downloads/details.aspx?familyid=0c323a12-6385-4666-ad39-a9516a8eda14) (KB2505935) (Important) | [Open XML File Format Converter for Mac](http://www.microsoft.com/downloads/details.aspx?familyid=0c323a12-6385-4666-ad39-a9516a8eda14) (KB2505935) (Important) | [Open XML File Format Converter for Mac](http://www.microsoft.com/downloads/details.aspx?familyid=0c323a12-6385-4666-ad39-a9516a8eda14) (KB2505935) (Important) |
| Other Office Software | ||||
| **Bulletin Identifier** | [**MS11-029**](http://go.microsoft.com/fwlink/?linkid=208524) | [**MS11-021**](http://go.microsoft.com/fwlink/?linkid=210121) | [**MS11-022**](http://go.microsoft.com/fwlink/?linkid=210727) | [**MS11-023**](http://go.microsoft.com/fwlink/?linkid=210206) |
| **Aggregate Severity Rating** | None | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) | None |
| Microsoft Excel Viewer Service Pack 2 | Not applicable | [Microsoft Excel Viewer Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=2d75786a-2368-4ef2-970b-fa2e57d63ca9) (KB2466158) (Important) | Not applicable | Not applicable |
| Microsoft PowerPoint Viewer 2007 Service Pack 2 | Not applicable | Not applicable | [Microsoft PowerPoint Viewer 2007 Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=6e23d3c3-2944-42ea-80b3-0663af60d0f1) (KB2464623) (Important) | Not applicable |
| Microsoft PowerPoint Viewer | Not applicable | Not applicable | [Microsoft PowerPoint Viewer](http://www.microsoft.com/downloads/details.aspx?familyid=44a703f5-b581-4900-bdbb-0f0e8d9bf0e6) (KB2519984) (Important) | Not applicable |
| Microsoft Office Compatibility Pack for Word, Excel, and PowerPoint 2007 File Formats Service Pack 2 | Not applicable | [Microsoft Office Compatibility Pack for Word, Excel, and PowerPoint 2007 File Formats Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=946cc611-4d75-4728-b9d3-1c8b557b02c2) (KB2466156) (Important) | [Microsoft Office Compatibility Pack for Word, Excel, and PowerPoint 2007 File Formats Service Pack 2](http://www.microsoft.com/downloads/details.aspx?familyid=913efc28-7deb-47b8-8c22-8eb5fc2631e4) (KB2464635) (Important) | Not applicable |
See also other software categories under this section, Affected Software and Download Locations, for more update files under the same bulletin identifier. This bulletin spans more than one software category.
Note for MS11-021
[1]For Microsoft Excel 2007 Service Pack 2, in addition to security update package KB2464583, customers also need to install the security update for Microsoft Office Compatibility Pack for Word, Excel, and PowerPoint 2007 File Formats Service Pack 2 (KB2466156) to be protected from the vulnerabilities described in this bulletin.
Note for MS11-022
Microsoft Security Update (kb2467173) Download
See also other software categories under this section, Affected Software and Download Locations, for more update files under the same bulletin identifier. This bulletin spans more than one software category.
Microsoft Server Software
| Microsoft Office Web Apps | |
|---|---|
| **Bulletin Identifier** | [**MS11-022**](http://go.microsoft.com/fwlink/?linkid=210727) |
| **Aggregate Severity Rating** | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) |
| Microsoft Office Web Apps | [Microsoft PowerPoint Web App](http://www.microsoft.com/downloads/details.aspx?familyid=9847dc05-7d4a-4a64-9e6a-622d3fa171f9) (KB2520047) (Important) |
See also other software categories under this section, Affected Software and Download Locations, for more update files under the same bulletin identifier. This bulletin spans more than one software category.
Microsoft Developer Tools and Software
| Microsoft Visual Studio | |
|---|---|
| **Bulletin Identifier** | [**MS11-025**](http://go.microsoft.com/fwlink/?linkid=209720) |
| **Aggregate Severity Rating** | [**Important**](http://go.microsoft.com/fwlink/?linkid=21140) |
| Microsoft Visual Studio .NET 2003 Service Pack 1 | [Microsoft Visual Studio .NET 2003 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=e9501082-a651-452b-8c1a-43987ffd3102) (KB2465373) (Important) |
| Microsoft Visual Studio 2005 Service Pack 1 | [Microsoft Visual Studio 2005 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=ee64d83b-6c06-4ccf-b12d-99e2a7a7b18d) (KB2538218) (Important) |
| Microsoft Visual Studio 2008 Service Pack 1 | [Microsoft Visual Studio 2008 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=e6a8e024-12ee-43d5-9aae-4c721505d6df) (KB2538241) (Important) |
| Microsoft Visual Studio 2010 and Microsoft Visual Studio 2010 Service Pack 1 | [Microsoft Visual Studio 2010](http://www.microsoft.com/downloads/details.aspx?familyid=7fd643a8-8e05-4d27-8853-33f79f01cb26) (KB2542054) (Important) [Microsoft Visual Studio 2010 Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=1a21c9db-dfa3-4a07-a1e0-89a8069b7c17) (KB2565057) (Important) |
| Microsoft Visual C++ 2005 Service Pack 1 | [Microsoft Visual C++ 2005 Service Pack 1 Redistributable Package](http://www.microsoft.com/downloads/details.aspx?familyid=ae2e1a40-7b45-4fe9-a20f-2ed2923aca62) (KB2538242) (Important) |
| Microsoft Visual C++ 2008 Service Pack 1 | [Microsoft Visual C++ 2008 Service Pack 1 Redistributable Package](http://www.microsoft.com/downloads/details.aspx?familyid=a821847e-4c44-45c0-9128-61c822bb3280) (KB2538243) (Important) |
| Microsoft Visual C++ 2010 and Microsoft Visual C++ 2010 Service Pack 1 | [Microsoft Visual C++ 2010 Redistributable Package](http://www.microsoft.com/downloads/details.aspx?familyid=fe558aed-9274-415f-8a0f-d9d8622fb35b) (KB2467173) (Important) [Microsoft Visual C++ 2010 Redistributable Package Service Pack 1](http://www.microsoft.com/downloads/details.aspx?familyid=7557d29b-731b-4abb-8815-2b87a4132efb) (KB2565063) (Important) |
Detection and Deployment Tools and Guidance
Security Central
Manage the software and security updates you need to deploy to the servers, desktop, and mobile computers in your organization. For more information see the TechNet Update Management Center. The TechNet Security Center provides additional information about security in Microsoft products. Consumers can visit Security At Home, where this information is also available by clicking 'Latest Security Updates'.
Security updates are available from Microsoft Update and Windows Update. Security updates are also available at the Microsoft Download Center. You can find them most easily by doing a keyword search for 'security update'.
For customers of Microsoft Office for Mac, Microsoft AutoUpdate for Mac can help keep your Microsoft software up to date. For more information about using Microsoft AutoUpdate for Mac, see Check for software updates automatically.
Finally, security updates can be downloaded from the Microsoft Update Catalog. The Microsoft Update Catalog provides a searchable catalog of content made available through Windows Update and Microsoft Update, including security updates, drivers and service packs. By searching using the security bulletin number (such as, 'MS07-036'), you can add all of the applicable updates to your basket (including different languages for an update), and download to the folder of your choosing. For more information about the Microsoft Update Catalog, see the Microsoft Update Catalog FAQ.
Detection and Deployment Guidance
Microsoft provides detection and deployment guidance for security updates. This guidance contains recommendations and information that can help IT professionals understand how to use various tools for detection and deployment of security updates. For more information, see Microsoft Knowledge Base Article 961747.
Microsoft Baseline Security Analyzer
The Microsoft Baseline Security Analyzer (MBSA) allows administrators to scan local and remote systems for missing security updates as well as common security misconfigurations. For more information about MBSA, visit Microsoft Baseline Security Analyzer.
Windows Server Update Services
By using Windows Server Update Services (WSUS), administrators can quickly and reliably deploy the latest critical updates and security updates for Microsoft Windows 2000 operating systems and later, Office XP and later, Exchange Server 2003, and SQL Server 2000 to Microsoft Windows 2000 and later operating systems.
For more information about how to deploy this security update using Windows Server Update Services, visit Windows Server Update Services.
System Center Configuration Manager 2007
Configuration Manager 2007 Software Update Management simplifies the complex task of delivering and managing updates to IT systems across the enterprise. With Configuration Manager 2007, IT administrators can deliver updates of Microsoft products to a variety of devices including desktops, laptops, servers, and mobile devices.
The automated vulnerability assessment in Configuration Manager 2007 discovers needs for updates and reports on recommended actions. The Software Update Management in Configuration Manager 2007 is built on Microsoft Windows Software Update Services (WSUS), a time-tested update infrastructure that is familiar to IT administrators worldwide. For more information about how administrators can use Configuration Manager 2007 to deploy updates, see Software Update Management. For more information about Configuration Manager, visit System Center Configuration Manager.
Systems Management Server 2003
Microsoft Systems Management Server (SMS) delivers a highly-configurable enterprise solution for managing updates. By using SMS, administrators can identify Windows-based systems that require security updates and to perform controlled deployment of these updates throughout the enterprise with minimal disruption to end users.
Note System Management Server 2003 is out of mainstream support as of January 12, 2010. For more information on product lifecycles, visit Microsoft Support Lifecycle. The next release of SMS, System Center Configuration Manager 2007, is now available; see the earlier section, System Center Configuration Manager 2007.
For more information about how administrators can use SMS 2003 to deploy security updates, see Scenarios and Procedures for Microsoft Systems Management Server 2003: Software Distribution and Patch Management. For information about SMS, visit the Microsoft Systems Management Server TechCenter.
Note SMS uses the Microsoft Baseline Security Analyzer to provide broad support for security bulletin update detection and deployment. Some software updates may not be detected by these tools. Administrators can use the inventory capabilities of SMS in these cases to target updates to specific systems. For more information about this procedure, see Deploying Software Updates Using the SMS Software Distribution Feature. Some security updates require administrative rights following a restart of the system. Administrators can use the Elevated Rights Deployment Tool (available in the SMS 2003 Administration Feature Pack) to install these updates.
Update Compatibility Evaluator and Application Compatibility Toolkit
Updates often write to the same files and registry settings required for your applications to run. This can trigger incompatibilities and increase the time it takes to deploy security updates. You can streamline testing and validating Windows updates against installed applications with the Update Compatibility Evaluator components included with Application Compatibility Toolkit.
The Application Compatibility Toolkit (ACT) contains the necessary tools and documentation to evaluate and mitigate application compatibility issues before deploying Microsoft Windows Vista, a Windows Update, a Microsoft Security Update, or a new version of Windows Internet Explorer in your environment.
Other Information
Microsoft Windows Malicious Software Removal Tool
Microsoft has released an updated version of the Microsoft Windows Malicious Software Removal Tool on Windows Update, Microsoft Update, Windows Server Update Services, and the Download Center.
Non-Security Updates on MU, WU, and WSUS
For information about non-security releases on Windows Update and Microsoft Update, please see:
- Microsoft Knowledge Base Article 894199: Description of Software Update Services and Windows Server Update Services changes in content. Includes all Windows content.
- Updates from Past Months for Windows Server Update Services. Displays all new, revised, and rereleased updates for Microsoft products other than Microsoft Windows.
Microsoft Active Protections Program (MAPP)
To improve security protections for customers, Microsoft provides vulnerability information to major security software providers in advance of each monthly security update release. Security software providers can then use this vulnerability information to provide updated protections to customers via their security software or devices, such as antivirus, network-based intrusion detection systems, or host-based intrusion prevention systems. To determine whether active protections are available from security software providers, please visit the active protections Web sites provided by program partners, listed in Microsoft Active Protections Program (MAPP) Partners.
Security Strategies and Community
Update Management Strategies
Security Guidance for Update Management provides additional information about Microsoft’s best-practice recommendations for applying security updates.
Obtaining Other Security Updates
Updates for other security issues are available from the following locations:
- Security updates are available from Microsoft Download Center. You can find them most easily by doing a keyword search for 'security update'.
- Updates for consumer platforms are available from Microsoft Update.
- You can obtain the security updates offered this month on Windows Update, from Download Center on Security and Critical Releases ISO CD Image files. For more information, see Microsoft Knowledge Base Article 913086.
IT Pro Security Community
Learn to improve security and optimize your IT infrastructure, and participate with other IT Pros on security topics in IT Pro Security Community.

Acknowledgments
Microsoft thanks the following for working with us to help protect customers:
- An anonymous researcher, working with VeriSign iDefense Labs, for reporting an issue described in MS11-018
- MITRE for working with us on an issue described in MS11-018
- Michal Zalewski of Google Inc. for working with us on an issue described in MS11-018
- David Bloom of Google Inc. for reporting two issues described in MS11-018
- Stephen Fewer of Harmony Security, working with TippingPoint'sZero Day Initiative, for reporting an issue described in MS11-018
- Alin Rad Pop of Secunia Research for reporting two issues described in MS11-021
- Muhammad Junaid Bohio of Telus Security Labs for reporting an issue described in MS11-021
- Aniway, working with TippingPoint'sZero Day Initiative, for reporting three issues described in MS11-021
- An anonymous researcher, working with VeriSign iDefense Labs, for reporting an issue described in MS11-021
- Rodrigo Rubira Branco of Check Point Vulnerability Discovery Team (VDT) for reporting an issue described in MS11-021
- An anonymous researcher, working with TippingPoint'sZero Day Initiative, for reporting an issue described in MS11-021
- An anonymous researcher, working with TippingPoint'sZero Day Initiative, for reporting an issue described in MS11-021
- TippingPoint'sZero Day Initiative for reporting three issues described in MS11-022
- Haifei Li of Fortinet's FortiGuard Labs for reporting an issue described in MS11-023
- An anonymous researcher, working with TippingPoint'sZero Day Initiative, for reporting an issue described in MS11-023
- Carsten Eiram of Secunia for working with us on an issue described in MS11-024
- The Google Security Team for working with us on an issue described in MS11-026
- Chris Ries of Carnegie Mellon University Information Security Office for reporting an issue described in MS11-027
- RadLSneak, working with iSIGHT Partners Global Vulnerability Partnership, for reporting an issue described in MS11-027
- Nicolas Joly and Chaouki Bekrar of VUPEN Threat Protection Program for reporting an issue described in MS11-029
- Neel Mehta of Google Inc. for reporting an issue described in MS11-030
- Jesse Ruderman of Mozilla for working with us on an issue described in MS11-031
- Adam Twardoch of Fontlab Ltd. for reporting an issue described in MS11-032
- Carsten Eiram of Secunia for reporting an issue described in MS11-033
- Tarjei Mandt of Norman for reporting 30 issues described in MS11-034
Support
- The affected software listed have been tested to determine which versions are affected. Other versions are past their support life cycle. To determine the support life cycle for your software version, visit Microsoft Support Lifecycle.
- Customers in the U.S. and Canada can receive technical support from Security Support or 1-866-PCSAFETY. There is no charge for support calls that are associated with security updates. For more information about available support options, see Microsoft Help and Support.
- International customers can receive support from their local Microsoft subsidiaries. There is no charge for support that is associated with security updates. For more information about how to contact Microsoft for support issues, visit International Help and Support.
Disclaimer
The information provided in the Microsoft Knowledge Base is provided 'as is' without warranty of any kind. Microsoft disclaims all warranties, either express or implied, including the warranties of merchantability and fitness for a particular purpose. In no event shall Microsoft Corporation or its suppliers be liable for any damages whatsoever including direct, indirect, incidental, consequential, loss of business profits or special damages, even if Microsoft Corporation or its suppliers have been advised of the possibility of such damages. Some states do not allow the exclusion or limitation of liability for consequential or incidental damages so the foregoing limitation may not apply.
Revisions
- V1.0 (April 12, 2011): Bulletin Summary published.
- V1.1 (April 13, 2011): For MS11-019, clarified the vulnerability description in the Executive Summary.
- V2.0 (April 15, 2011): For MS11-032, raised the Exploitability Index assessment rating for CVE-2011-0034 to '1 - Consistent exploit code likely.'
- V3.0 (April 21, 2011): Revised to offer the rereleased security update for MS11-025.
- V3.1 (April 27, 2011): For MS11-024, corrected the Exploitability Index to add CVE-2010-4701 as a vulnerability addressed by this update. This is an informational change only.
- V4.0 (May 16, 2011): MS11-018 bulletin rereleased to reoffer the update for Internet Explorer 7 on supported editions of Windows XP and Windows Server 2003. This is a detection change only. There were no changes to the binaries. Only affected customers will be offered the update. Customers who have installed the update manually and customers running configurations not targeted by the change to detection logic do not need to take any action.
- V5.0 (June 14, 2011): For MS11-025, reoffered the update for Microsoft Visual Studio 2005 Service Pack 1, Microsoft Visual Studio 2008 Service Pack 1, Microsoft Visual Studio 2010, Microsoft Visual C++ 2005 Service Pack 1 Redistributable Package, and Microsoft Visual C++ 2008 Service Pack 1 Redistributable Package. Customers who have previously installed this update should install the new packages on the affected systems.
- V6.0 (August 9, 2011): For MS11-025, added Microsoft Visual Studio 2010 Service Pack 1 (KB2565057) and Microsoft Visual C++ 2010 Redistributable Package Service Pack 1 (KB2565063) as Affected Software.
- V6.1 (October 26, 2011): For MS11-028, corrected Server Core installation applicability for .NET Framework 4 on Windows Server 2008 R2 for x64-based Systems.
Built at 2014-04-18T13:49:36Z-07:00
-->Security Bulletin
Vulnerability in Microsoft Foundation Class (MFC) Library Could Allow Remote Code Execution (2500212)
Published: April 12, 2011 Updated: October 9, 2018
Version: 5.0
General Information
Executive Summary
This security update resolves a publicly disclosed vulnerability in certain applications built using the Microsoft Foundation Class (MFC) Library. The vulnerability could allow remote code execution if a user opens a legitimate file associated with such an affected application, and the file is located in the same network folder as a specially crafted library file. For an attack to be successful, a user must visit an untrusted remote file system location or WebDAV share and open a document from this location that is then loaded by the affected application.
This security update is rated Important for all supported editions of Microsoft Visual Studio and Microsoft Visual C++ Redistributable Package. For more information, see the subsection, Affected and Non-Affected Software, in this section.
The security update addresses the vulnerability by correcting the manner in which applications built using MFC load external libraries. For more information about the vulnerability, see the Frequently Asked Questions (FAQ) subsection for the specific vulnerability entry under the next section, Vulnerability Information.
Caterpillar serial numbers and year. Serial numbers contain a piece of equipment's model number and factory of manufacture. Caterpillar Inc.' S products, which range from heavy machinery to engines, are manufactured in over 20 countries, including the United States, Canada, China, Germany and Mexico. For more advanced parts manuals search capabilities, try using Service Information Systems (SIS). Jun 02, 2017 Caterpillar vin number decoding. Discussion in 'Tractor/Loader/Backhoes' started by NHGus, Jun 29, 2010. How can the answer be improved? Find your Cat model by using this serial number prefix guide to easily identifyyour engine. Sorted for generators, industrial, marine and trucks Get our Mobile App!
Recommendation. The majority of customers have automatic updating enabled and will not need to take any action because this security update will be downloaded and installed automatically. Customers who have not enabled automatic updating need to check for updates and install this update manually. For information about specific configuration options in automatic updating, see Microsoft Knowledge Base Article 294871.
For administrators and enterprise installations, or end users who want to install this security update manually, Microsoft recommends that customers apply the update at the earliest opportunity using update management software, or by checking for updates using the Microsoft Update service.
See also the section, Detection and Deployment Tools and Guidance, later in this bulletin.
18 rows Rollei Repairs By Harry Fleenor Oceanside Camera Repair 909 Aviation Blvd. 4 Manhattan Beach, Ca 90266 310 374 6506 - email - harry@rolleirepairs.com. 
Known Issues.Microsoft Knowledge Base Article 2500212 documents the currently known issues that customers may experience when installing this security update. The article also documents recommended solutions for these issues.
Affected and Non-Affected Software
The following software have been tested to determine which versions or editions are affected. Other versions or editions are either past their support life cycle or are not affected. To determine the support life cycle for your software version or edition, visit Microsoft Support Lifecycle.
Affected Software
| Operating System | Maximum Security Impact | Aggregate Severity Rating | Bulletins Replaced by this Update |
|---|---|---|---|
| Microsoft Visual Studio .NET 2003 Service Pack 1 (KB2465373) | Remote Code Execution | Important | MS09-035 |
| Microsoft Visual Studio 2005 Service Pack 1 (KB2538218) | Remote Code Execution | Important | MS09-035 |
| Microsoft Visual Studio 2008 Service Pack 1 (KB2538241) | Remote Code Execution | Important | MS09-035 |
| Microsoft Visual Studio 2010 (KB2542054) | Remote Code Execution | Important | None |
| Microsoft Visual Studio 2010 Service Pack 1 (KB2565057) | Remote Code Execution | Important | None |
| Microsoft Visual C++ 2005 Service Pack 1 Redistributable Package (KB2538242) | Remote Code Execution | Important | MS09-035 |
| Microsoft Visual C++ 2008 Service Pack 1 Redistributable Package (KB2538243) | Remote Code Execution | Important | MS09-035 |
| Microsoft Visual C++ 2010 Redistributable Package (KB2467173) | Remote Code Execution | Important | None |
| Microsoft Visual C++ 2010 Redistributable Package Service Pack 1 (KB2565063) | Remote Code Execution | Important | None |
| Microsoft Exchange Server 2010 Service Pack 3 (KB2565063) | Remote Code Execution | Important | None |
| Microsoft Exchange Server 2013 (KB2565063) | Remote Code Execution | Important | None |
| Microsoft Exchange Server 2016 (KB2565063) | Remote Code Execution | Important | None |
| Affected Software | MFC Insecure Library Loading Vulnerability - CVE-2010-3190 | Aggregate Severity Rating |
|---|---|---|
| Microsoft Visual Studio .NET 2003 Service Pack 1 | Important Remote Code Execution | Important |
| Microsoft Visual Studio 2005 Service Pack 1 | Important Remote Code Execution | Important |
| Microsoft Visual Studio 2008 Service Pack 1 | Important Remote Code Execution | Important |
| Microsoft Visual Studio 2010 | Important Remote Code Execution | Important |
| Microsoft Visual Studio 2010 Service Pack 1 | Important Remote Code Execution | Important |
| Microsoft Visual C++ 2005 Service Pack 1 Redistributable Package | Important Remote Code Execution | Important |
| Microsoft Visual C++ 2008 Service Pack 1 Redistributable Package | Important Remote Code Execution | Important |
| Microsoft Visual C++ 2010 Redistributable Package | Important Remote Code Execution | Important |
| Microsoft Visual C++ 2010 Redistributable Package Service Pack 1 | Important Remote Code Execution | Important |
| Inclusion in Future Service Packs | None |
| Deployment | |
| Installing without user intervention | VS7.1sp1-KB2465373-X86 /q |
| Installing without restarting | VS7.1sp1-KB2465373-X86 /norestart |
| Update log file | VS7.1SP1-KB2465373-X86-intl-msi.0.log VS7.1SP1-KB2465373-X86-intl-wrapper.log |
| Further information | For detection and deployment, see the earlier section, Detection and Deployment Tools and Guidance. |
| Restart Requirement | |
| Restart required? | In some cases, this update does not require a restart. If the required files are being used, this update will require a restart. If this behavior occurs, a message appears that advises you to restart. |
| Hotpatching | Not applicable |
| Removal Information | Use Add or Remove Programs tool in Control Panel. |
| File Information | See Microsoft Knowledge Base Article 2465373 |
| Registry Key Verification | HKEY_LOCAL_MACHINESoftwareMicrosoftUpdatesVisual Studio7.1M2465373 'Installed' = dword:1 |
Deployment Information
Installing the Update
You can install the update from the appropriate download link in the Affected and Non-Affected Software section. If you installed your application from a server location, the server administrator must instead update the server location with the administrative update and deploy that update to your system.
This security update requires that Windows Installer 3.1 or later be installed on the system.
To install the 3.1 or later version of Windows Installer, visit one of the following Microsoft Web sites:
This security update supports the following setup switches.
| Switch | Description |
| /? or /h or /help | Display usage dialog box. |
| Setup Mode | |
| /q[n b r f] | Sets user interface level n - No UI b - Basic UI r - Reduced UI f - Full UI |
| /quiet | Same as /q |
| /passive | Same as /qb |
| Install Options | |
| /extract [directory] | Extract the package to the specified directory. |
| /uninstall or /u | Uninstall this update. |
| /addsource or /as | Specifies the source path of the product msi. This option may be used when installing the the update results in a prompt to insert the installation source media for the product. For example: <update executable> /addsource 'C:Product MSIVisual Studioenuvs_setup.msi' /addsource 'C:Product MSINetNetfx.msi' |
| Restart Options | |
| /norestart | Do not restart after the installation is complete |
| /promptrestart | Prompts the user for restart if necessary |
| /forcerestart | Restart the computer after installation if necessary (e.g. if a file is locked or in use) |
| Logging Options | |
| /l[i w e a r u c m o p v x + ! *] <LogFile> | i - Status messages w - Nonfatal warnings e - All error messages a - Start up of actions r - Action-specific records u - User requests c - Initial UI parameters m - Out-of-memory or fatal exit information o - Out-of-disk-space messages p - Terminal properties v - Verbose output x - Extra debugging information + - Append to existing log file ! - Flush each line to the log * - Log all information, except for v and x options |
| /log <LogFile> | Equivalent of /l* <LogFile> |
| /sendreport | Send installation data for this update to Microsoft as a Watson report. No personally identifiable information is sent. |
| Inclusion in Future Service Packs | None |
| Deployment | |
| Installing without user intervention | VS80sp1-KB2538218-v2-X86-INTL.exe /qn |
| Installing without restarting | VS80sp1-KB2538218-v2-X86-INTL.exe /norestart |
| Update log file | Not applicable |
| Further information | For detection and deployment, see the earlier section, Detection and Deployment Tools and Guidance. For features you can selectively install, see the Office Features for Administrative Installations subsection in this section. |
| Restart Requirement | |
| Restart required? | In some cases, this update does not require a restart. If the required files are being used, this update will require a restart. If this behavior occurs, a message appears that advises you to restart. |
| Hotpatching | Not applicable |
| Removal Information | Use Add or Remove Programs tool in Control Panel. |
| File Information | See Microsoft Knowledge Base Article 2538218 |
| Registry Key Verification | HKEY_LOCAL_MACHINESOFTWAREMicrosoftUpdatesMicrosoft Visual Studio 2005 Professional Edition - ENUKB2538218 'Installed' = dword:1 |
Deployment Information
Installing the Update
You can install the update from the appropriate download link in the Affected and Non-Affected Software section. If you installed your application from a server location, the server administrator must instead update the server location with the administrative update and deploy that update to your system. For more information about Administrative Installation Points, refer to the Office Administrative Installation Point information in the Detection and Deployment Tools and Guidance subsection.
This security update requires that Windows Installer 2.0 or later be installed on the system. All supported versions of Windows include Windows Installer 2.0 or a later version.
To install the latest version of Windows Installer, visit the following Microsoft Web site:
For more information about the terminology that appears in this bulletin, such as hotfix, see Microsoft Knowledge Base Article 824684.
This security update supports the following setup switches.
| Switch | Description |
| /? or /h or /help | Display usage dialog box. |
| Setup Mode | |
| /q[n b r f] | Sets user interface level n - No UI b - Basic UI r - Reduced UI f - Full UI |
| /quiet | Same as /q |
| /passive | Same as /qb |
| Install Options | |
| /extract [directory] | Extract the package to the specified directory. |
| /uninstall or /u | Uninstall this update. |
| /addsource or /as | Specifies the source path of the product msi. This option may be used when installing the the update results in a prompt to insert the installation source media for the product. For example: <update executable> /addsource 'C:Product MSIVisual Studioenuvs_setup.msi' /addsource 'C:Product MSINetNetfx.msi' |
| Restart Options | |
| /norestart | Do not restart after the installation is complete |
| /promptrestart | Prompts the user for restart if necessary |
| /forcerestart | Always restart the computer after installation |
| Logging Options | |
| /l[i w e a r u c m o p v x + ! *] <LogFile> | i - Status messages w - Nonfatal warnings e - All error messages a - Start up of actions r - Action-specific records u - User requests c - Initial UI parameters m - Out-of-memory or fatal exit information o - Out-of-disk-space messages p - Terminal properties v - Verbose output x - Extra debugging information + - Append to existing log file ! - Flush each line to the log * - Log all information, except for v and x options |
| /log <LogFile> | Equivalent of /l* <LogFile> |
| /sendreport | Send installation data for this update to Microsoft as a Watson report. No personally identifiable information is sent. |
Ms11 025 Fix
**Note** You can combine these switches into one command. For backward compatibility, the security update also supports many of the setup switches that the earlier version of the Setup program uses. For more information about the supported installation switches, see [Microsoft Knowledge Base Article 262841](http://support.microsoft.com/kb/262841). **Removing the Update** To remove this security update, use the Add or Remove Programs tool in Control Panel. **Note** When you remove this update, you may be prompted to insert the 2007 Microsoft Office CD in the CD drive. Additionally, you may not have the option to uninstall the update from the Add or Remove Programs tool in Control Panel. There are several possible causes for this issue. For more information about the removal, see [Microsoft Knowledge Base Article 903771](http://support.microsoft.com/kb/903771). **Verifying that the Update Has Been Applied** - **Microsoft Baseline Security Analyzer** To verify that a security update has been applied to an affected system, you may be able to use the Microsoft Baseline Security Analyzer (MBSA) tool. See the “Microsoft baseline Security Analyzer” heading under the section, Microsoft Detection and Deployment Tools and Guidance. - **File Version Verification** **Note** Because there are several versions and editions of Microsoft Windows, the following steps may be different on your system. If they are, see your product documentation to complete these steps. 1. Click **Start**, and then click **Search**. 2. In the Search Results pane, click All files and folders under Search Companion. 3. In the **All or part of the file name** box, type a file name from the appropriate file information table, and then click **Search**. 4. In the list of files, right-click a file name from the appropriate file information table, and then click **Properties**. **Note** Depending on the edition of the operating system, or the programs that are installed on your system, some of the files that are listed in the file information table may not be installed. 5. On the **Version** tab, determine the version of the file that is installed on your system by comparing it to the version that is documented in the appropriate file information table. **Note** Attributes other than the file version may change during installation. Comparing other file attributes to the information in the file information table is not a supported method of verifying that the update has been applied. Also, in certain cases, files may be renamed during installation. If the file or version information is not present, use one of the other available methods to verify update installation. #### Microsoft Visual Studio 2008 Service Pack 1 **Reference Table** The following table contains the security update information for this software. You can find additional information in the subsection, **Deployment Information**, in this section.| Inclusion in Future Service Packs | None |
| Deployment | |
| Installing without user intervention | VS90SP1-KB2538241-x86.exe /q |
| Installing without restarting | VS90SP1-KB2538241-x86.exe /norestart |
| Update log file | Not applicable |
| Further information | For detection and deployment, see the earlier section, Detection and Deployment Tools and Guidance. For features you can selectively install, see the Office Features for Administrative Installations subsection in this section. |
| Restart Requirement | |
| Restart required? | In some cases, this update does not require a restart. If the required files are being used, this update will require a restart. If this behavior occurs, a message appears that advises you to restart. |
| Hotpatching | Not applicable |
| Removal Information | Use Add or Remove Programs tool in Control Panel. |
| File Information | See Microsoft Knowledge Base Article 2538241 |
| Registry Key Verification | HKEY_LOCAL_MACHINESOFTWAREMicrosoftUpdatesMicrosoft Visual Studio Team System 2008 Team Suite - ENUKB2538241 'ThisVersionInstalled' = REG_SZ:'Y' |
Deployment Information
Installing the Update
You can install the update from the appropriate download link in the Affected and Non-Affected Software section. If you installed your application from a server location, the server administrator must instead update the server location with the administrative update and deploy that update to your system. For more information about Administrative Installation Points, refer to the Office Administrative Installation Point information in the Detection and Deployment Tools and Guidance subsection.
This security update requires that Windows Installer 2.0 or later be installed on the system. All supported versions of Windows include Windows Installer 2.0 or a later version.
To install the latest version of Windows Installer, visit the following Microsoft Web site:
For more information about the terminology that appears in this bulletin, such as hotfix, see Microsoft Knowledge Base Article 824684.
This security update supports the following setup switches.
| Switch | Description |
| /? or /h or /help | Display usage dialog box. |
| Setup Mode | |
| /q[n b r f] | Sets user interface level n - No UI b - Basic UI r - Reduced UI f - Full UI |
| /quiet | Same as /q |
| /passive | Same as /qb |
| Install Options | |
| /extract [directory] | Extract the package to the specified directory. |
| /uninstall or /u | Uninstall this update. |
| /addsource or /as | Specifies the source path of the product msi. This option may be used when installing the the update results in a prompt to insert the installation source media for the product. For example: <update executable> /addsource 'C:Product MSIVisual Studioenuvs_setup.msi' /addsource 'C:Product MSINetNetfx.msi' |
| Restart Options | |
| /norestart | Do not restart after the installation is complete |
| /promptrestart | Prompts the user for restart if necessary |
| /forcerestart | Always restart the computer after installation |
| Logging Options | |
| /l[i w e a r u c m o p v x + ! *] <LogFile> | i - Status messages w - Nonfatal warnings e - All error messages a - Start up of actions r - Action-specific records u - User requests c - Initial UI parameters m - Out-of-memory or fatal exit information o - Out-of-disk-space messages p - Terminal properties v - Verbose output x - Extra debugging information + - Append to existing log file ! - Flush each line to the log * - Log all information, except for v and x options |
| /log <LogFile> | Equivalent of /l* <LogFile> |
| /sendreport | Send installation data for this update to Microsoft as a Watson report. No personally identifiable information is sent. |
| Inclusion in Future Service Packs | Microsoft Visual Studio 2010 Service Pack 1 |
| Deployment | |
| Installing without user intervention | For Microsoft Visual Studio 2010: VS10-KB2542054-x86.exe /q |
| For Microsoft Visual Studio 2010 Service Pack 1: VS10SP1-KB2565057-x86.exe /q | |
| Installing without restarting | For Microsoft Visual Studio 2010: VS10-KB2542054-x86.exe /norestart |
| For Microsoft Visual Studio 2010 Service Pack 1: VS10SP1-KB2565057-x86.exe /norestart | |
| Update log file | Not applicable |
| Further information | For detection and deployment, see the earlier section, Detection and Deployment Tools and Guidance. For features you can selectively install, see the Office Features for Administrative Installations subsection in this section. |
| Restart Requirement | |
| Restart required? | In some cases, this update does not require a restart. If the required files are being used, this update will require a restart. If this behavior occurs, a message appears that advises you to restart. |
| Hotpatching | Not applicable |
| Removal Information | Use Add or Remove Programs tool in Control Panel. |
| File Information | For Microsoft Visual Studio 2010: See Microsoft Knowledge Base Article 2542054 |
| For Microsoft Visual Studio 2010 Service Pack 1: See Microsoft Knowledge Base Article 2565057 | |
| Registry Key Verification | For Microsoft Visual Studio 2010: HKEY_LOCAL_MACHINESOFTWAREMicrosoftUpdatesMicrosoft Visual Studio Team System 2010 Team Suite - ENUKB2542054 'ThisVersionInstalled' = REG_SZ:'Y' |
| For Microsoft Visual Studio 2010 Service Pack 1: HKEY_LOCAL_MACHINESoftwareMicrosoftDevDivVSServicing10.0 |
Deployment Information
Installing the Update
You can install the update from the appropriate download link in the Affected and Non-Affected Software section. If you installed your application from a server location, the server administrator must instead update the server location with the administrative update and deploy that update to your system. For more information about Administrative Installation Points, refer to the Office Administrative Installation Point information in the Detection and Deployment Tools and Guidance subsection.
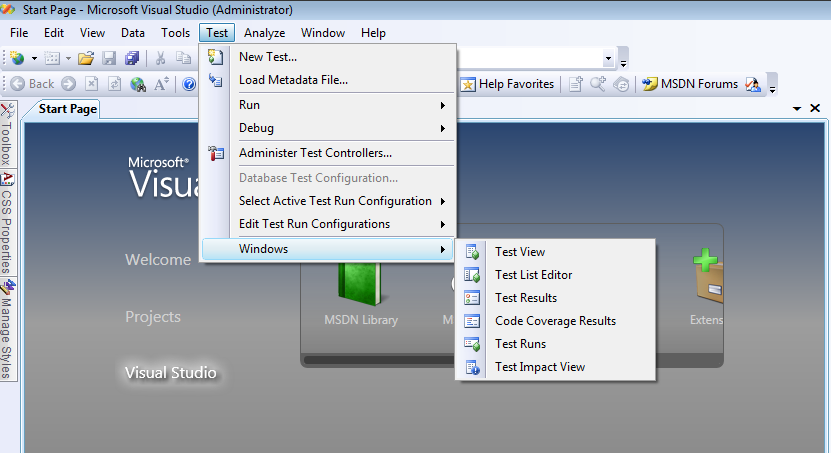
This security update requires that Windows Installer 2.0 or later be installed on the system. All supported versions of Windows include Windows Installer 2.0 or a later version.
To install the latest version of Windows Installer, visit the following Microsoft Web site:
For more information about the terminology that appears in this bulletin, such as hotfix, see Microsoft Knowledge Base Article 824684.
Kb2467173 Download
This security update supports the following setup switches.
| Switch | Description |
| /? or /h or /help | Display usage dialog box. |
| Setup Mode | |
| /q[n b r f] | Sets user interface level n - No UI b - Basic UI r - Reduced UI f - Full UI |
| /quiet | Same as /q |
| /passive | Same as /qb |
| Install Options | |
| /extract [directory] | Extract the package to the specified directory. |
| /uninstall or /u | Uninstall this update. |
| /addsource or /as | Specifies the source path of the product msi. This option may be used when installing the the update results in a prompt to insert the installation source media for the product. For example: <update executable> /addsource 'C:Product MSIVisual Studioenuvs_setup.msi' /addsource 'C:Product MSINetNetfx.msi' |
| Restart Options | |
| /norestart | Do not restart after the installation is complete |
| /promptrestart | Prompts the user for restart if necessary |
| /forcerestart | Always restart the computer after installation |
| Logging Options | |
| /l[i w e a r u c m o p v x + ! *] <LogFile> | i - Status messages w - Nonfatal warnings e - All error messages a - Start up of actions r - Action-specific records u - User requests c - Initial UI parameters m - Out-of-memory or fatal exit information o - Out-of-disk-space messages p - Terminal properties v - Verbose output x - Extra debugging information + - Append to existing log file ! - Flush each line to the log * - Log all information, except for v and x options |
| /log <LogFile> | Equivalent of /l* <LogFile> |
| /sendreport | Send installation data for this update to Microsoft as a Watson report. No personally identifiable information is sent. |
| Inclusion in Future Service Packs | None |
| Deployment | |
| Installing without user intervention | For Microsoft Visual C++ 2005 Service Pack 1 Redistributable Package (x86): vcredist_x86 /q For Microsoft Visual C++ 2005 Service Pack 1 Redistributable Package (x64): vcredist_x64 /q For Microsoft Visual C++ 2005 Service Pack 1 Redistributable Package (IA64): vcredist_ia64 /q |
| Installing without restarting | For Microsoft Visual C++ 2005 Service Pack 1 Redistributable Package (x86): vcredist_x86 /r:n For Microsoft Visual C++ 2005 Service Pack 1 Redistributable Package (x64): vcredist_x64 /r:n For Microsoft Visual C++ 2005 Service Pack 1 Redistributable Package (IA64): vcredist_ia64 /r:n |
| Update log file | Not applicable |
| Further information | For detection and deployment, see the earlier section, Detection and Deployment Tools and Guidance |
| Restart Requirement | |
| Restart required? | This update does not require a restart. |
| Hotpatching | Not applicable |
| Removal Information | Use Add or Remove Programs tool in Control Panel. |
| File Information | See Microsoft Knowledge Base Article 2538242 |
| Registry Key Verification | For Microsoft Visual C++ 2005 Service Pack 1 Redistributable Package (x86): {710f4c1c-cc18-4c49-8cbf-51240c89a1a2} For Microsoft Visual C++ 2005 Service Pack 1 Redistributable Package (x64): {ad8a2fa1-06e7-4b0d-927d-6e54b3d31028} For Microsoft Visual C++ 2005 Service Pack 1 Redistributable Package (IA64): {c2f60bda-462a-4a72-8e4d-ca431a56e9ea} For instructions on how to verify installation using product codes, see Microsoft Knowledge Base Article 974653. |
Deployment Information
Installing the Update
You can install the update from the appropriate download link in the Affected and Non-Affected Software section. If you installed your application from a server location, the server administrator must instead update the server location with the administrative update and deploy that update to your system. For more information about Administrative Installation Points, refer to the Office Administrative Installation Point information in the Detection and Deployment Tools and Guidance subsection.
This security update requires that Windows Installer 2.0 or later be installed on the system. All supported versions of Windows include Windows Installer 2.0 or a later version.
To install the latest version of Windows Installer, visit the following Microsoft Web site:
For more information about the terminology that appears in this bulletin, such as hotfix, see Microsoft Knowledge Base Article 824684.
This security update supports the following setup switches.
| Switch | Description |
|---|---|
| /? | Displays the command-line options. |
| Setup Modes | |
| /q[:u :a] | /q - Specifies quiet mode, or suppresses prompts. /q:u - Specifies user-quiet mode, which presents some dialog boxes to the user. /q:a - Specifies administrator-quiet mode, which does not present any dialog boxes to the user. |
| Install Options | |
| /C | Extracts the files without installing them. If /t: path is not specified, you are prompted for a target folder. |
| /T:path | Specifies the target folder for extracting files. |
| /C:path | Specifies the UNC path and name of the Setup .inf or .exe file. |
| /n:v | No version checking - Install the package over any previous version. |
| Restart Options | |
| /r:n | Never restarts the computer after installation. |
| /r:i | Prompts the user to restart the computer if a restart is required, except when used with /q:a. |
| /r:a | Always restarts the computer after installation. |
| /r:s | Restarts the computer after installation without prompting the user. |
| Inclusion in Future Service Packs | None |
| Deployment | |
| Installing without user intervention | For Microsoft Visual C++ 2008 Service Pack 1 Redistributable Package (x86): vcredist_x86 /q For Microsoft Visual C++ 2008 Service Pack 1 Redistributable Package (x64): vcredist_x64 /q For Microsoft Visual C++ 2008 Service Pack 1 Redistributable Package (IA64): vcredist_ia64 /q |
| Installing without restarting | For Microsoft Visual C++ 2008 Service Pack 1 Redistributable Package (x86): vcredist_x86 /r:n For Microsoft Visual C++ 2008 Service Pack 1 Redistributable Package (x64): vcredist_x64 /r:n For Microsoft Visual C++ 2008 Service Pack 1 Redistributable Package (IA64): vcredist_ia64 /r:n |
| Update log file | Not applicable |
| Further information | For detection and deployment, see the earlier section, Detection and Deployment Tools and Guidance |
| Restart Requirement | |
| Restart required? | This update does not require a restart. |
| Hotpatching | Not applicable |
| Removal Information | Use Add or Remove Programs tool in Control Panel. |
| File Information | See Microsoft Knowledge Base Article 2538243 |
| Registry Key Verification | For Microsoft Visual C++ 2008 Service Pack 1 Redistributable Package (x86): HKEY_LOCAL_MACHINESOFTWAREMicrosoftDevDivVCServicing9.0RED1033SP1x86IndividualFixes2538241 'Install' = dword:1 For Microsoft Visual C++ 2008 Service Pack 1 Redistributable Package (x64): HKEY_LOCAL_MACHINESOFTWAREMicrosoftDevDivVCServicing9.0RED1033SP1amd64IndividualFixes2538241 'Install' = dword:1 For Microsoft Visual C++ 2008 Service Pack 1 Redistributable Package (x64): HKEY_LOCAL_MACHINESOFTWAREMicrosoftDevDivVCServicing9.0RED1033SP1 ia64IndividualFixes2538241 'Install' = dword:1 |
Deployment Information
Installing the Update
You can install the update from the appropriate download link in the Affected and Non-Affected Software section. If you installed your application from a server location, the server administrator must instead update the server location with the administrative update and deploy that update to your system. For more information about Administrative Installation Points, refer to the Office Administrative Installation Point information in the Detection and Deployment Tools and Guidance subsection.
This security update requires that Windows Installer 2.0 or later be installed on the system. All supported versions of Windows include Windows Installer 2.0 or a later version.
To install the latest version of Windows Installer, visit the following Microsoft Web site:
For more information about the terminology that appears in this bulletin, such as hotfix, see Microsoft Knowledge Base Article 824684.
This security update supports the following setup switches.
| Switch | Description |
|---|---|
| /? | Displays the command-line options. |
| Setup Modes | |
| /q[:u :a] | /q - Specifies quiet mode, or suppresses prompts. /q:u - Specifies user-quiet mode, which presents some dialog boxes to the user. /q:a - Specifies administrator-quiet mode, which does not present any dialog boxes to the user. |
| Install Options | |
| /C | Extracts the files without installing them. If /t: path is not specified, you are prompted for a target folder. |
| /T:path | Specifies the target folder for extracting files. |
| /C:path | Specifies the UNC path and name of the Setup .inf or .exe file. |
| /n:v | No version checking - Install the package over any previous version. |
| Restart Options | |
| /r:n | Never restarts the computer after installation. |
| /r:i | Prompts the user to restart the computer if a restart is required, except when used with /q:a. |
| /r:a | Always restarts the computer after installation. |
| /r:s | Restarts the computer after installation without prompting the user. |
| Inclusion in Future Service Packs | Microsoft Visual C++ 2010 Service Pack 1 Redistributable Package |
| Deployment | |
| Installing without user intervention | For Microsoft Visual C++ 2010 Redistributable Package and Microsoft Visual C++ 2010 Redistributable Package Service Pack 1 (x86): vcredist_x86 /q For Microsoft Visual C++ 2010 Redistributable Package and Microsoft Visual C++ 2010 Redistributable Package Service Pack 1 (x64): vcredist_x64 /q For Microsoft Visual C++ 2010 Redistributable Package and Microsoft Visual C++ 2010 Redistributable Package Service Pack 1 (IA64): vcredist_ia64 /q |
| Installing without restarting | For Microsoft Visual C++ 2010 Redistributable Package and Microsoft Visual C++ 2010 Redistributable Package Service Pack 1 (x86): vcredist_x86 /norestart For Microsoft Visual C++ 2010 Redistributable Package and Microsoft Visual C++ 2010 Redistributable Package Service Pack 1 (x64): vcredist_x64 /norestart For Microsoft Visual C++ 2010 Redistributable Package and Microsoft Visual C++ 2010 Redistributable Package Service Pack 1 (IA64): vcredist_ia64 /norestart |
| Update log file | Not applicable |
| Further information | For detection and deployment, see the earlier section, Detection and Deployment Tools and Guidance |
| Restart Requirement | |
| Restart required? | This update does not require a restart. |
| Hotpatching | Not applicable |
| Removal Information | Use Add or Remove Programs tool in Control Panel. |
| File Information | For Microsoft Visual C++ 2010 Redistributable Package: See Microsoft Knowledge Base Article 2467173 |
| For Microsoft Visual C++ 2010 Redistributable Package Service Pack 1: See Microsoft Knowledge Base Article 2565063 | |
| Registry Key Verification | For Microsoft Visual C++ 2010 Redistributable Package (x86): HKEY_LOCAL_MACHINESOFTWAREMicrosoftVisualStudio10.0VCVCRedistx86KB2467173 'Install' = dword:1 For Microsoft Visual C++ 2010 Redistributable Package (x64): HKEY_LOCAL_MACHINESOFTWAREMicrosoftVisualStudio10.0VCVCRedistx64KB2467173 'Install' = dword:1 For Microsoft Visual C++ 2010 Redistributable Package (IA64): HKEY_LOCAL_MACHINESOFTWAREMicrosoftVisualStudio10.0VCVCRedistIA64KB2467173 'Install' = dword:1 |
| For Microsoft Visual C++ 2010 Redistributable Package Service Pack 1 (x86): HKEY_LOCAL_MACHINESOFTWARE MicrosoftDevDivvcServicing10.0redx861033 'Install' = dword:1 For Microsoft Visual C++ 2010 Redistributable Package Service Pack 1 (x64): HKEY_LOCAL_MACHINESOFTWARE MicrosoftDevDivvcServicing10.0redamd641033 'Install' = dword:1 For Microsoft Visual C++ 2010 Redistributable Package Service Pack 1 (IA64): HKEY_LOCAL_MACHINESOFTWARE MicrosoftDevDivvcServicing10.0redia641033 'Install' = dword:1 |
Deployment Information
Installing the Update
You can install the update from the appropriate download link in the Affected and Non-Affected Software section. If you installed your application from a server location, the server administrator must instead update the server location with the administrative update and deploy that update to your system. For more information about Administrative Installation Points, refer to the Office Administrative Installation Point information in the Detection and Deployment Tools and Guidance subsection.
This security update requires that Windows Installer 2.0 or later be installed on the system. All supported versions of Windows include Windows Installer 2.0 or a later version.
Kb2467173 Download Windows 10
To install the latest version of Windows Installer, visit the following Microsoft Web site:
For more information about the terminology that appears in this bulletin, such as hotfix, see Microsoft Knowledge Base Article 824684.
This security update supports the following setup switches.
| Switch | Description |
| /? or /h or /help | Display usage dialog box. |
| Setup Mode | |
| /q[n b r f] | Sets user interface level n - No UI b - Basic UI r - Reduced UI f - Full UI |
| /quiet | Same as /q |
| /passive | Same as /qb |
| Install Options | |
| /extract [directory] | Extract the package to the specified directory. |
| /uninstall or /u | Uninstall this update. |
| /addsource or /as | Specifies the source path of the product msi. This option may be used when installing the the update results in a prompt to insert the installation source media for the product. For example: <update executable> /addsource 'C:Product MSIVisual Studioenuvs_setup.msi' /addsource 'C:Product MSINetNetfx.msi' |
| Restart Options | |
| /norestart | Do not restart after the installation is complete |
| /promptrestart | Prompts the user for restart if necessary |
| /forcerestart | Always restart the computer after installation |
| Logging Options | |
| /l[i w e a r u c m o p v x + ! *] <LogFile> | i - Status messages w - Nonfatal warnings e - All error messages a - Start up of actions r - Action-specific records u - User requests c - Initial UI parameters m - Out-of-memory or fatal exit information o - Out-of-disk-space messages p - Terminal properties v - Verbose output x - Extra debugging information + - Append to existing log file ! - Flush each line to the log * - Log all information, except for v and x options |
| /log <LogFile> | Equivalent of /l* <LogFile> |
| /sendreport | Send installation data for this update to Microsoft as a Watson report. No personally identifiable information is sent. |
Kb2467173 Download
**Note** You can combine these switches into one command. For backward compatibility, the security update also supports many of the setup switches that the earlier version of the Setup program uses. For more information about the supported installation switches, see [Microsoft Knowledge Base Article 262841](http://support.microsoft.com/kb/262841). **Removing the Update** To remove this security update, use the Add or Remove Programs tool in Control Panel. **Note** When you remove this update, you may be prompted to insert the 2007 Microsoft Office CD in the CD drive. Additionally, you may not have the option to uninstall the update from the Add or Remove Programs tool in Control Panel. There are several possible causes for this issue. For more information about the removal, see [Microsoft Knowledge Base Article 903771](http://support.microsoft.com/kb/903771). **Verifying that the Update Has Been Applied** - **Microsoft Baseline Security Analyzer** To verify that a security update has been applied to an affected system, you may be able to use the Microsoft Baseline Security Analyzer (MBSA) tool. See the “Microsoft baseline Security Analyzer” heading under the section, Microsoft Detection and Deployment Tools and Guidance. - **File Version Verification** **Note** Because there are several versions and editions of Microsoft Windows, the following steps may be different on your system. If they are, see your product documentation to complete these steps. 1. Click **Start**, and then click **Search**. 2. In the Search Results pane, click All files and folders under Search Companion. 3. In the **All or part of the file name** box, type a file name from the appropriate file information table, and then click **Search**. 4. In the list of files, right-click a file name from the appropriate file information table, and then click **Properties**. **Note** Depending on the edition of the operating system, or the programs that are installed on your system, some of the files that are listed in the file information table may not be installed. 5. On the **Version** tab, determine the version of the file that is installed on your system by comparing it to the version that is documented in the appropriate file information table. **Note** Attributes other than the file version may change during installation. Comparing other file attributes to the information in the file information table is not a supported method of verifying that the update has been applied. Also, in certain cases, files may be renamed during installation. If the file or version information is not present, use one of the other available methods to verify update installation. ### Other Information #### Microsoft Active Protections Program (MAPP) To improve security protections for customers, Microsoft provides vulnerability information to major security software providers in advance of each monthly security update release. Security software providers can then use this vulnerability information to provide updated protections to customers via their security software or devices, such as antivirus, network-based intrusion detection systems, or host-based intrusion prevention systems. To determine whether active protections are available from security software providers, please visit the active protections Web sites provided by program partners, listed in [Microsoft Active Protections Program (MAPP) Partners](http://go.microsoft.com/fwlink/?linkid=215201). #### Support - Customers in the U.S. and Canada can receive technical support from [Security Support](http://go.microsoft.com/fwlink/?linkid=21131) or 1-866-PCSAFETY. There is no charge for support calls that are associated with security updates. For more information about available support options, see [Microsoft Help and Support](http://support.microsoft.com/). - International customers can receive support from their local Microsoft subsidiaries. There is no charge for support that is associated with security updates. For more information about how to contact Microsoft for support issues, visit the [International Support Web site](http://go.microsoft.com/fwlink/?linkid=21155). #### Disclaimer The information provided in the Microsoft Knowledge Base is provided 'as is' without warranty of any kind. Microsoft disclaims all warranties, either express or implied, including the warranties of merchantability and fitness for a particular purpose. In no event shall Microsoft Corporation or its suppliers be liable for any damages whatsoever including direct, indirect, incidental, consequential, loss of business profits or special damages, even if Microsoft Corporation or its suppliers have been advised of the possibility of such damages. Some states do not allow the exclusion or limitation of liability for consequential or incidental damages so the foregoing limitation may not apply. #### Revisions - V1.0 (April 12, 2011): Bulletin published. - V1.1 (April 12, 2011): Clarified the update FAQ, 'I am a third-party application developer and I use Visual C++. How do I update my application?' - V2.0 (April 21, 2011): Rereleased bulletin to reoffer the updates to address a detection issue. There were no changes to the security update files in this bulletin. Customers who have already successfully updated their systems do not need to reinstall this update. - V2.1 (April 27, 2011): Corrected the bulletin replacement information and clarified the update FAQ entry, 'Will I be offered this update even if I have no suitable attack vectors on my system?' - V3.0 (June 14, 2011): Reoffered the update for Microsoft Visual Studio 2005 Service Pack 1, Microsoft Visual Studio 2008 Service Pack 1, Microsoft Visual Studio 2010, Microsoft Visual C++ 2005 Service Pack 1 Redistributable Package, and Microsoft Visual C++ 2008 Service Pack 1 Redistributable Package. Customers who have previously installed this update should install the new packages on the affected systems. - V4.0 (August 9, 2011): Added Microsoft Visual Studio 2010 Service Pack 1 (KB2565057) and Microsoft Visual C++ 2010 Redistributable Package Service Pack 1 (KB2565063) as Affected Software. See the update FAQ for details. Also corrected the file verification information for Microsoft Visual C++ 2005 Service Pack 1 Redistributable Package, Microsoft Visual C++ 2008 Service Pack 1 Redistributable Package, and Microsoft Visual C++ 2010 Redistributable Package. - V4.1 (November 23, 2011): Corrected the installation switches and switch tables for Microsoft Visual C++ 2010 Redistributable Package and Microsoft Visual C++ 2010 Redistributable Package Service Pack 1. This is an informational change only. - V4.2 (January 24, 2012): Added an entry to the update FAQ to announce a detection change for KB2538242, KB2538243, KB2467173, KB2538218, KB2538241, and KB2542054 to correct an installation issue. This is a detection change only. There were no changes to the security update files. Customers who have already successfully updated their systems do not need to take any action. - V4.3 (March 13, 2012): Added an entry to the update FAQ to announce a detection change for KB2565063 and KB2565057 to correct an installation issue. This is a detection change only. There were no changes to the security update files. Customers who have already successfully updated their systems do not need to take any action.- V5.0 (October 9, 2018): Added Exchange Servers to the Affected Products table. Customers who have any supported Exchange Server installed (Microsoft Exchange Server 2010 Service Pack 3, Microsoft Exchange Server 2013, Microsoft Exchange Server 2016) should reinstall KB2565063.Built at 2014-04-18T13:49:36Z-07:00